The year 2026 marks a historic funeral in the world of cybersecurity: the death of the long-lived session cookie. For over three decades, these small strings of data have been the “silent workhorse” of the internet, allowing users to stay logged into their favorite SaaS platforms, banking portals, and internal corporate tools without re-entering credentials for every single action. However, the very convenience that made cookies ubiquitous has also made them the primary target for modern adversaries.
As organizations successfully move toward a Managing Identity in a “Passkey-First” World,1 they are effectively hardening the “front door” of the enterprise. Phishing a passkey is exponentially harder than phishing a password. Yet, cybercriminals are adaptive. Instead of trying to break the door down, they are now waiting for a legitimate user to open it, then stealing the “all-access pass”, the session token, that is generated immediately after a successful login.
This shift in the threat landscape necessitates a fundamental change in how we define identity. We can no longer rely on a single point of authentication. Instead, the resilient enterprise must move toward a model of continuous behavioral verification (CBV), where trust is not a static state granted at login, but a dynamic score that is recalculated with every keystroke, mouse movement, and data request.
The Anatomy of the Session Hijack
To understand why the session cookie is failing, one must look at the industrialization of “infostealer” malware. In the current threat environment, attackers deploy lightweight, highly specialized malware designed to bypass traditional antivirus software. Once inside a victim’s machine, these tools do not search for files; they search for the browser’s “cookie jar.”
By extracting active session tokens, an attacker can perform a “Session Hijack” or “Pass-the-Cookie” attack. Because the server believes the attacker is the already-authenticated user, it does not prompt for a password or Multi-Factor Authentication (MFA). To the system, the attacker is the user.
The Beyond the Leak: Analyzing the Real-World Exploitation of Stolen Credentials Using Honeypots2 real-world exploitation of stolen credentials, including capture of session activity, showing that compromised identity material (usernames/passwords) leads to successful authentication attempts against systems in practice. It provides evidence of attacker use of credentials and session data in active exploits. This confirms that even the most robust MFA can be bypassed if the session itself is not protected.
The BISO’s New Mandate: Governing the Session
This technical vulnerability has profound business implications. As previously covered in Emutare’s analysis of The Rise of the BISO,3 the Business Information Security Officer is tasked with ensuring that security does not impede business velocity. However, a session hijack allows an attacker to move laterally through business units, accessing sensitive financial data or customer records with the perceived authority of a trusted employee.
In a “Resilient by Design” enterprise, the BISO must move the conversation from “authentication” to “authorization.” It is not enough to know who logged in; the business must continuously verify that the actions being taken are consistent with that identity. If a marketing manager who typically spends their day in a CRM suddenly starts bulk-downloading source code from a repository, the session should be invalidated immediately, regardless of whether they have a valid cookie.
The Science of Behavioral Biometrics
How do we verify identity without constantly pestering the user for a thumbprint or a code? The answer lies in behavioral biometrics. This technology analyzes the unique patterns in how a human interacts with a device. Just as every person has a unique physical fingerprint, they also have a unique “digital gait.”
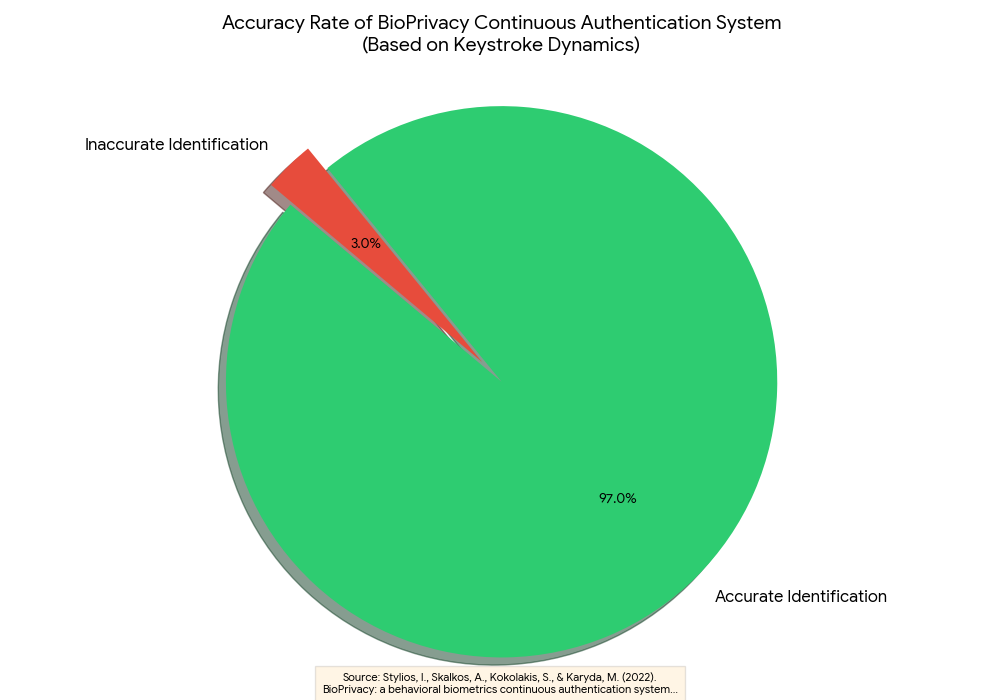
Peer reviewed research BioPrivacy: a behavioral biometrics continuous authentication system based on keystroke dynamics and touch gestures4 on keystroke dynamics shows that typing rhythm alone can be highly effective for continuous authentication. In controlled experimental settings, machine learning models trained on features such as dwell time and flight time achieved accuracy rates of about 97 percent. The study also reported strong true accept rates and low false accept rates, indicating that legitimate users were reliably recognized while impostors were correctly rejected.
In the event of a session hijack, an attacker (or an automated bot) will inevitably display different behavioral patterns. An AI bot moves with a mathematical precision that humans cannot replicate; a human attacker from a different geographic region may use different keyboard shortcuts or navigation paths. Continuous Behavioral Verification (CBV) detects these anomalies in real-time and triggers a “step-up” authentication or terminates the session before data can be exfiltrated.
The Agentic AI Complication
The transition to CBV is further complicated by the rise of agentic AI. As we explored in our discussion on The Resilient by Design Enterprise,5 organizations are increasingly using autonomous agents to automate complex tasks. These agents require their own sessions and identities.
The challenge is that these agents act like “super-users” with high-velocity interaction patterns. If a security system is tuned to look for “human” behavior, it might flag a legitimate AI agent as a malicious bot. Conversely, an attacker could use a compromised AI agent to carry out a breach, hiding within the high-volume traffic.
The solution is the creation of “Behavioral Profiles” for both humans and machines. Just as we baseline human behavior, we must baseline the “normal” behavior of an AI agent. This requires deep integration between the BISO, the IT team, and the developers of these AI systems to ensure that security policies are “aware” of the agent’s intended function.
Strategic Implementation: A Roadmap for 2026
For business leaders and IT professionals, moving away from the “static cookie” model requires a multi-year strategy. This is not a “rip and replace” operation, but an evolution of the existing identity stack.
Phase 1: Shortening the Window of Risk
The easiest way to reduce session risk is to reduce the life-cycle of the session token. Historically, cookies could last for days or even weeks to provide a “seamless” experience. In 2026, this is a liability.
- Action: Implement “Just-in-Time” (JIT) sessions that expire after a period of inactivity or after a specific high-value task is completed.
- Metric: Track “Average Session Duration” and aim to align it with actual work patterns.
Phase 2: Implementing Device-Bound Tokens
To prevent a token stolen on one machine from being used on another, organizations must move toward “Device-Bound” session tokens. These use cryptographic keys stored in a device’s Trusted Platform Module (TPM) to “lock” the session to the hardware.
- Action: Deploy browsers and enterprise applications that support Token Binding (RFC 8471) or similar standards.
- Alignment: This aligns with our previous guidance on Passkey-First strategies, as both rely on hardware-backed security.
Phase 3: The Deployment of Passive CBV
The most critical phase is the integration of passive behavioral monitoring. This layer sits quietly in the background, collecting telemetry without interrupting the user’s workflow.
- Action: Invest in an Identity Threat Detection and Response (ITDR) platform that incorporates behavioral biometrics.
- Outcome: This creates a “trust score” for every active session. As long as the score is high, the user is never prompted for MFA. If the score drops (e.g., due to a change in typing rhythm or an unusual API call), the system automatically triggers a re-authentication.
The Economic Case for Behavioral Trust
While some may view continuous verification as an added expense, the economic reality of 2026 tells a different story. The World Economic Forum’s Global Cybersecurity Outlook 20266 indicates that the average cost of a breach involving compromised identities has risen significantly, largely due to the speed at which AI-enabled attackers can move once inside a network.
Furthermore, the “friction” of traditional MFA is a hidden cost. Every time an employee has to stop work to find their phone and enter a six-digit code, productivity is lost. By moving to a behavioral model, organizations can actually reduce the number of active interruptions for legitimate users while simultaneously increasing security for the enterprise. It is the rare “win-win” in the cybersecurity world: better protection and a better user experience.
Overcoming the Privacy Hurdle
One common concern with behavioral verification is the perceived invasion of privacy. Does the company now “own” the rhythm of my heartbeat or the speed of my typing?
To maintain a Resilient by Design culture, transparency is paramount. Organizations must be clear that behavioral biometrics do not “record” what a user is typing (which would be a keylogger), but rather how they are typing. The data is typically converted into an anonymized mathematical hash that cannot be reversed to reconstruct the original input.
The BISO plays a crucial role here in collaborating with legal and HR departments to ensure that these tools comply with global privacy standards like GDPR and CCPA. When employees understand that these tools protect their own professional identity from being hijacked and misused, the cultural adoption becomes much smoother.
Conclusion: The Future of Sovereign Identity
The transition from session cookies to continuous behavioral verification represents the next great leap in digital sovereignty. We are moving away from a world where “possession” of a digital token equals identity, and into a world where identity is defined by the unique, inimitable essence of our behavior.
For the modern enterprise, this shift is the cornerstone of resilience. It allows business units to move at the speed of AI while ensuring that the “actors” within the system are truly who they claim to be. By embedding these principles into the organization, as advocated in our work on The Rise of the BISO, leaders can build a future that is not only secure but fundamentally robust.
The era of the “one-and-done” login is over. The era of continuous trust has begun.
As the era of session cookies ends, Emutare empowers your enterprise to lead the shift toward continuous trust. Our AI-Driven Process Automation and Software Development services help you baseline agentic behavior and build secure, resilient identities. We offer advanced SIEM and XDR Deployment alongside ITDR solutions to integrate passive behavioral monitoring into your security stack. Through expert Cybersecurity Advisory and Infrastructure Architecture, we ensure your transition to hardware-backed, continuous verification is seamless.
References
- Emutare. (2026). Beyond the Password: Managing Identity in a “Passkey-First” World. https://insights.emutare.com/beyond-the-password-managing-identity-in-a-passkey-first-world/ ↩︎
- Rabzelj, M., & Sedlar, U. (2025). Beyond the leak: Analyzing the real-world exploitation of stolen credentials using honeypots. Sensors, 25(12), 3676. https://doi.org/10.3390/s25123676 ↩︎
- Emutare. (2026). The Rise of the BISO: Embedding Security into Business Units. https://insights.emutare.com/the-rise-of-the-biso-embedding-security-into-business-units/ ↩︎
- Stylios, I., Skalkos, A., Kokolakis, S., & Karyda, M. (2022). BioPrivacy: a behavioral biometrics continuous authentication system based on keystroke dynamics and touch gestures. Information & Computer Security, 30(5), 687-704. https://www.sciencedirect.com/org/science/article/abs/pii/S2056496122000113? ↩︎
- Emutare. (2025). The Resilient by Design Enterprise: Unifying Strategy, Speed, and Security. https://insights.emutare.com/the-resilient-by-design-enterprise-unifying-strategy-speed-and-security/ ↩︎
- World Economic Forum. (2026).Global Cybersecurity Outlook 2026. https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf ↩︎
Related Blog Posts
- Certificate-Based Authentication for Users and Devices: A Comprehensive Security Strategy
- IoT Security Challenges in Enterprise Environments
- Future of IoT Security: Regulations and Technologies
- Risk-Based Authentication: Adaptive Security
- IoT Threat Modeling and Risk Assessment: Securing the Connected Ecosystem
- Red Team vs. Blue Team vs. Purple Team Exercises: Strengthening Your Organization’s Security Posture
- AI Security: Protecting Machine Learning Systems

