The year 2026 has brought a definitive shift in the digital landscape. We are no longer merely defending perimeters; we are managing an ecosystem of high-speed, automated interactions where trust is the only currency that matters. For business leaders and IT professionals, the challenge has evolved from simple threat mitigation to the pursuit of total operational resilience. This shift is driven by three converging forces: the rise of agentic AI threats, the looming shadow of quantum computing, and a regulatory environment that has grown increasingly intolerant of “compliance by checkbox.”
To survive in this environment, organizations must look beyond the individual silos of their security stack and embrace a unified strategy. This strategy rests on three critical pillars: rigorous security architecture, modernized identity management through Public Key Infrastructure (PKI), and a strict adherence to governance frameworks like APRA CPS 234. By integrating these elements, firms can move from a reactive posture to a resilient one, ensuring that their digital foundations are not just compliant, but genuinely unbreakable.
The Architecture of Modern Trust
Everything begins with the blueprint. In an era where 29% of vulnerabilities now show evidence of exploitation before a CVE is even officially published, as noted in recent 2026 cybersecurity forecasts from SentinelOne,1 the traditional “build now, secure later” model is a recipe for disaster. Security must be baked into the very DNA of the enterprise through continuous review.
As previously covered in Emutare’s Security Architecture Review Processes,2 a robust review is not a one-time event but a living part of the development lifecycle. This process identifies structural weaknesses before they can be weaponized by AI-driven attackers who now use autonomous agents to conduct reconnaissance at machine speeds. A well-executed architecture review ensures that security controls are not just present, but effective in the context of the specific business risks the organization faces.
Practical implementation of this pillar requires a shift toward “Architecture as Code.” Business leaders should empower their IT teams to:
- Automate Guardrails: Use cloud-native tools to enforce architectural standards automatically.
- Conduct Sandbox Testing: Before any AI agent or new microservice enters production, it must be validated in a sandboxed environment to prevent cascading failures.
- Map Data Flows: Understand exactly how sensitive information moves between internal systems and third-party vendors.
PKI: The Quiet Engine of Identity and Encryption
If architecture is the blueprint, then Public Key Infrastructure (PKI) is the engine that powers secure communications and identity. However, many organizations are currently operating with “legacy engines” that are ill-equipped for the demands of 2026. The shortening of certificate lifecycles and the expansion of machine identities (IoT devices, bots, and containers) have placed an immense strain on manual PKI processes.
The risks of neglecting this area are significant. To learn more about the complexities of modern identity management, one should consult Emutare’s Comprehensive Guide to PKI Design and Management.3 This guide highlights why automation and crypto-agility are no longer optional. With NIST having finalized post-quantum standards, 2026 has become the “mandate year” for quantum-safe migration. Organizations that fail to automate their certificate management now will find themselves unable to pivot when legacy encryption algorithms are eventually broken by quantum advances.
Google Cloud’s 2026 AI Agent Trends Report4 identifies “agentic AI” as the mandatory evolution for digital survival. They argue that successful organizations are replacing manual workflows with autonomous agents that move from instruction-based tasks to intent-based computing. By creating “digital assembly lines,” firms can automate relentlessly while using AI agents to verify and maintain trust at every interaction point. This is particularly critical for financial institutions where the integrity of every transaction depends on the strength of the underlying cryptographic keys.
Regulatory Rigor: The APRA CPS 234 Standard
In Australia, the “gold standard” for this level of security is the Australian Prudential Regulation Authority’s (APRA) CPS 234. While it was initially designed to ensure that APRA-regulated entities maintain information security capabilities commensurate with their vulnerabilities, its influence has expanded. It now serves as a global benchmark for how financial institutions should govern their digital assets.
As explored in Emutare’s APRA CPS 234 Compliance Guide,5 the standard places the ultimate responsibility for information security squarely on the Board of Directors. This is not a technicality; it is a fundamental shift in governance. Boards are now required to ensure that their organizations have a clearly defined information security policy, a robust testing program, and the ability to notify the regulator of any material security incident within 72 hours.
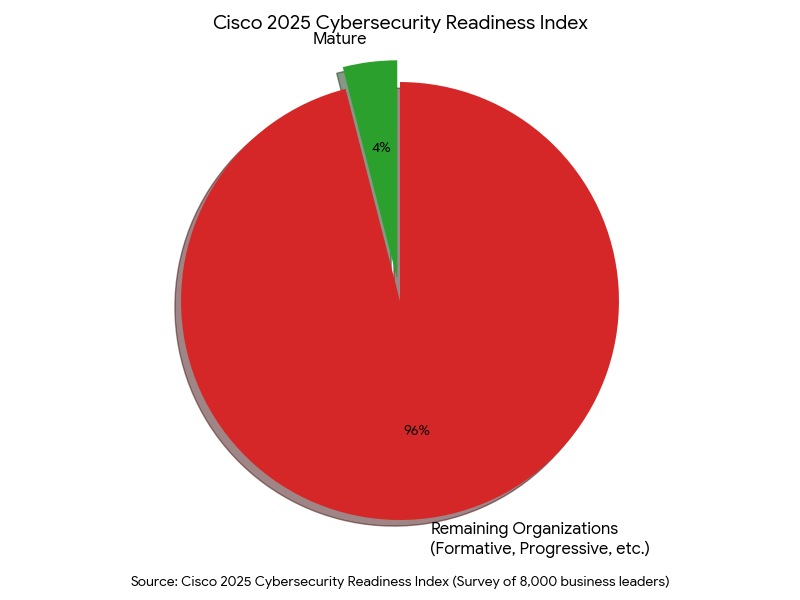
This regulatory pressure is mirrored globally. According to the Cisco 2025 Cybersecurity Readiness Index,6 which surveyed 8,000 business leaders across 30 global markets, the disconnect between transformation and security is quantified by several stark metrics; only 4% of companies worldwide have reached a “Mature” level of readiness. This means that 96% of organizations are still struggling to build a security posture capable of defending their digital advancements. APRA CPS 234 forces this connection by demanding that security is not a separate IT project but a core component of operational risk management.
Integrating the Pillars: Actionable Guidance for Leaders
To bridge the gap between technical execution and regulatory compliance, business leaders should focus on three practical steps:
1. Align Architecture with Compliance Outcomes
Don’t treat an architecture review and a compliance audit as separate tasks. An architecture review should be used to provide the “evidence of effectiveness” that regulators like APRA demand. When your architects review a system, they should specifically look for the controls required by CPS 234, such as restricted access to sensitive data and the presence of logging and monitoring.
2. Modernize PKI for Resilience, Not Just Security
Move away from manual certificate tracking in spreadsheets. Implementation should focus on:
- Centralized Management: Use a platform that provides a single pane of glass for all certificates across cloud and on-premise environments.
- Crypto-Agility: Ensure your systems can support multiple cryptographic algorithms simultaneously, allowing for a phased transition to post-quantum standards.
- Short-Lived Certificates: Reduce the “blast radius” of a compromised key by moving toward certificates that expire in days or weeks, rather than years.
3. Elevate the Board’s “Cyber IQ”
Governance is only as strong as the people overseeing it. Under CPS 234, the Board must be actively involved. This means IT professionals must translate technical risks (like PKI outages or architectural flaws) into business impact statements. Instead of talking about “RSA-2048 deprecation,” talk about the “risk of total transaction failure in the event of a cryptographic breach.”
The Resilience Gap: A Warning for 2026
The statistics for 2026 show a widening “resilience gap.” While large organizations have reduced their reports of inadequate resilience from 13% in 2022 to just 7% in 2025, smaller enterprises and mid-market firms are falling behind. This is often because they view security as an expense to be minimized rather than a foundation to be built upon.
However, the cost of a breach is only going up. A data breach in 2026 costs a financial firm an average of $6.4 million, and for healthcare providers, that number jumps to $11.2 million. These figures, provided in the 2026 Cybersecurity Report by SentinelOne,7 highlight the reality that “good enough” security is a relic of the past.
Conclusion: A Unified Front
True cybersecurity in the modern age is not about any single tool or regulation. It is about the synergy between a well-designed architecture, a secure and agile identity framework (PKI), and a disciplined governance structure (CPS 234).
When these three pillars work in harmony, they create a “Triple Crown of Resilience.” Architecture ensures that systems are built to withstand the unexpected; PKI ensures that every interaction within those systems is authenticated and encrypted; and CPS 234 ensures that the entire process is overseen by a leadership team that understands its critical importance.
The path forward requires a commitment to continuous improvement. As the threats from AI and quantum computing evolve, so too must our defenses. By focusing on these core principles, organizations can do more than just survive the digital age (they can lead it with confidence).
Secure Your Future with Emutare
Don’t let legacy systems compromise your resilience. Emutare provides the expert guidance necessary to master the “Triple Crown of Resilience”. Our comprehensive services include rigorous Security Architecture Reviews to identify structural weaknesses before they are weaponized. We specialize in modernizing PKI Design and Management to ensure quantum-safe automation and identity security. Additionally, our APRA CPS 234 Compliance experts help your Board navigate complex regulatory demands with ease. Build a foundation that is genuinely unbreakable.
References
- SentinelOne. (2026). Key Cyber Security Statistics for 2026. https://www.sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics/ ↩︎
- Emutare. (2025). Security Architecture Review Processes: A Comprehensive Guide to Modern Cybersecurity Assessment. https://insights.emutare.com/security-architecture-review-processes-a-comprehensive-guide-to-modern-cybersecurity-assessment/ ↩︎
- Emutare. (2025). Public Key Infrastructure (PKI) Design and Management: A Comprehensive Guide for Modern Organizations. https://insights.emutare.com/public-key-infrastructure-pki-design-and-management-a-comprehensive-guide-for-modern-organizations/ ↩︎
- Google Cloud. (2026). Ai Agent Trends 2026 Report. https://services.google.com/fh/files/misc/google_cloud_ai_agent_trends_2026_report.pdf ↩︎
- Emutare. (2025). APRA CPS 234: Compliance Guide for Financial Institutions. https://insights.emutare.com/apra-cps-234-compliance-guide-for-financial-institutions/ ↩︎
- Cisco. (2025). 2025 Cisco Cybersecurity Readiness Index. https://newsroom.cisco.com/c/dam/r/newsroom/en/us/interactive/cybersecurity-readiness-index/2025/documents/2025_Cisco_Cybersecurity_Readiness_Index.pdf ↩︎
- SentinelOne. (2026). Key Cyber Security Statistics for 2026. https://www.sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics/ ↩︎
Related Blog Posts
- Board Reporting on Cybersecurity: What Executives Need to Know
- Multi-Factor Authentication: Comparing Different Methods
- Secrets Management in DevOps Environments: Securing the Modern Software Development Lifecycle
- Zero Trust for Remote Work: Practical Implementation
- DevSecOps for Cloud: Integrating Security into CI/CD
- Customer Identity and Access Management (CIAM): The Competitive Edge for Australian Businesses
- Infrastructure as Code Security Testing: Securing the Foundation of Modern IT

