In the digital landscape of 2026, the concept of “sovereignty” has migrated from the borders of nations to the servers of small businesses. For a long time, the prevailing wisdom for growing companies was to outsource everything to the “hyperscalers”, large, centralized cloud providers that offered convenience at the cost of control. However, a series of global shifts has forced a re-evaluation of this trade-off.
Digital sovereignty is no longer an abstract political ambition; it is a practical necessity for operational survival. It is the ability for a business to operate, make decisions, and access its own data without being contingent on external entities whose interests or geographic jurisdictions may not align with theirs. As we move deeper into this year, small and medium enterprises (SMEs) are discovering that true resilience requires more than just good backups, it requires “digital autonomy.”
The Three Pillars of Modern Sovereignty
To understand why this matters now, we must look at the three interconnected layers that define a sovereign business:
- Data Sovereignty: The assurance that your data is subject to the laws of the country in which it is located and that you have absolute, frictionless control over its migration.
- Operational Sovereignty: The ability to maintain business continuity even if a major cloud vendor suffers a massive outage or unilaterally changes its service terms.
- Technology Sovereignty: The capacity to innovate using tools (like AI models) that do not lock you into a single proprietary ecosystem or use your data to train a competitor’s product.
The urgency is driven by a hardening regulatory environment. With the EU Data Act reaching full application and the Cybersecurity Maturity Model Certification (CMMC) 2.0 impacting any SME in the defense supply chain, the cost of “un-sovereign” data is becoming a direct hit to the bottom line. The Australian Signals Directorate (ASD) provides the technical blueprints and security standards that define sovereign cloud in Australia. Through its Blueprint for Secure Cloud,1 the ASD mandates that “Protected” level workloads maintain strict data residency within Australian borders. Their guidelines require “Sovereign Operations,” ensuring that cloud administration and data management are handled locally to maintain national jurisdictional control.
The Hyperscaler Trap: Convenience vs. Lock-in
For many small businesses, the primary threat to sovereignty is “vendor lock-in.” When a company relies entirely on a single provider for their email, CRM, file storage, and AI processing, they create a single point of failure. If that provider experiences a 48-hour outage or doubles their pricing, the business is effectively held hostage.
To learn more about how to structure a defense that avoids these pitfalls, it is useful to review our previous guidance on the Security Technology Stack for Growing Businesses.2 A sovereign-conscious stack prioritizes interoperability. Instead of a monolithic suite, it utilizes “best-of-breed” tools that allow for data portability.
The risk of lock-in has expanded into the realm of Artificial Intelligence. Many SMEs are unknowingly sacrificing their intellectual property by feeding sensitive internal documents into public AI models to generate reports. This is a violation of digital sovereignty at its most fundamental level. Modern sovereign solutions now allow businesses to run localized, “private” AI instances where the data never leaves the company’s controlled infrastructure.
Strategic Infrastructure: The Rise of Sovereign Clouds
The solution for the 2026 small business is not to build their own data center in a basement, that would be a regression in security and efficiency. Instead, the answer lies in the Sovereign Cloud.
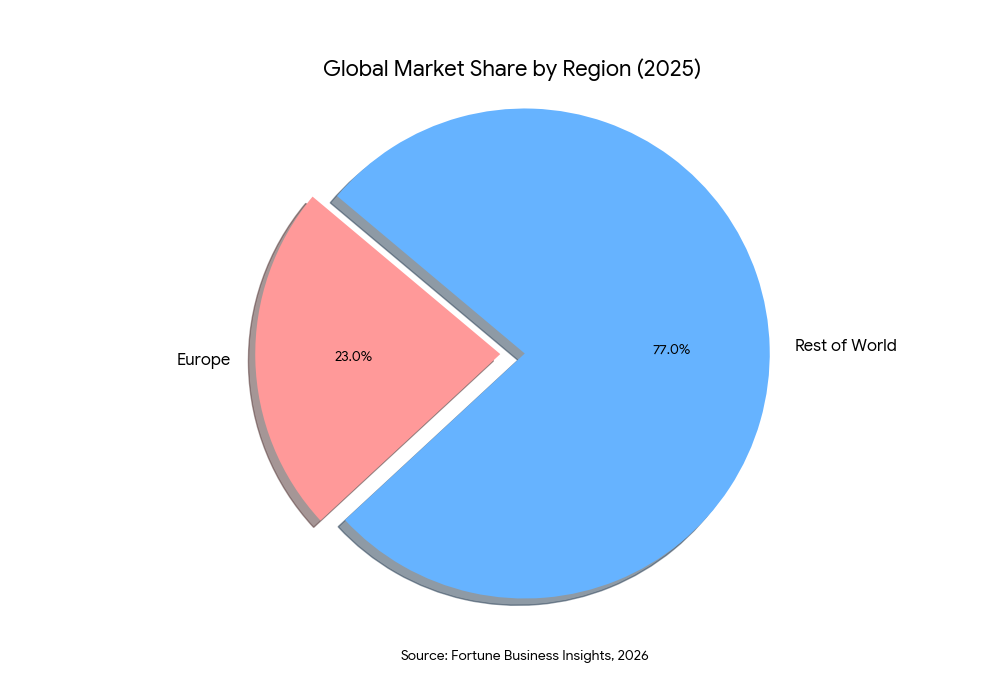
Unlike general-purpose public clouds, sovereign clouds are designed to adhere to the specific legal and security standards of a particular region. According to Fortune Business Insights,3 Europe dominated this market in 2025, accounting for 23% of the global share, largely due to strict data residency mandates. For an SME, using a sovereign cloud provider means your customer data doesn’t just “exist in the cloud”; it exists in a specific legal jurisdiction where you have clear rights of recovery and protection.
As previously covered in our discussion on Risk-Based Vulnerability Prioritization,4 knowing where your data resides is a prerequisite for effective risk management. If you don’t have sovereign control over your infrastructure, you cannot accurately assess the risk of a breach or a service interruption. You are essentially outsourcing your risk management to a third party that may not prioritize your small business during a global crisis.
Decentralized Storage: The New Frontier of Resilience
One of the most intriguing developments in 2026 is the adoption of decentralized data storage by small businesses. Rather than trusting a single server, data is encrypted, shredded, and distributed across a peer-to-peer network of nodes. This “distributed” approach eliminates the single point of failure and makes it nearly impossible for a single entity to seize or block your data.
Research titled Digital Sovereignty in the Era of Industry 5.05 highlights that decentralized architectures are no longer just for blockchain enthusiasts. They are becoming a core strategy for “Quality 5.0,” which combines proactive predictive analytics with cyber resilience. For an SME, this means that even if a major regional network goes down, their critical “shredded” data can be reconstituted from other points on the globe, ensuring near-perfect availability.
Practical Steps Toward Digital Sovereignty
Achieving sovereignty is a gradual process of reclaiming control. Business leaders and IT professionals should follow these implementation steps:
1. Map Your Data Residency
Perform a comprehensive audit of where your data is stored. Is your payroll data in a US-based cloud? Is your customer list in a server in Singapore? Documenting this is the first step toward compliance with local laws and ensuring you can get your data back if the vendor relationship sours.
2. Implement “Local-First” Workflows
Where possible, choose software that prioritizes “local-first” architecture. This means the software runs on your local machine and only uses the cloud for syncing and backup. If the internet goes down, your team stays productive. This is the ultimate form of operational sovereignty.
3. Audit Your Directory and Access Controls
Your identity services are the gatekeepers of your sovereignty. As covered in our guide on Directory Services Security: Active Directory and Beyond,6 moving toward a more decentralized or “self-sovereign” identity model can prevent a single compromised cloud account from taking down your entire business.
4. Diversify Your Cloud Portfolio
Avoid the “All Your Eggs in One Basket” syndrome. Use a hybrid-cloud or multi-cloud strategy where sensitive workloads remain on a sovereign cloud, while less critical, high-compute tasks are offloaded to public providers.
Conclusion
Digital sovereignty in 2026 is about choice. It is about the freedom to move your business as you see fit, without being locked into a vendor’s roadmap or a foreign government’s data laws. For small businesses, this autonomy is a powerful competitive differentiator. Customers are increasingly looking for partners they can trust, and being able to say “Your data never leaves our sovereign control” is a compelling value proposition.
By strategically choosing your tech stack, prioritizing data residency, and embracing the resilience of decentralized systems, you can ensure that your business remains the master of its own digital destiny. The path to growth is no longer just about adoption; it is about intentional, sovereign ownership.
In 2026, digital sovereignty is your competitive edge. At Emutare, we empower small businesses to reclaim their digital destiny through intentional technology ownership. Our experts help you move beyond the hyperscaler trap by implementing “best-of-breed” security stacks and resilient directory services. Whether you need to map complex data residency or transition to a secure sovereign cloud, we provide the strategic roadmap your organization requires. Don’t outsource your risk management to third parties. Contact Emutare today to build a sovereign-conscious infrastructure that ensures your data, power, and autonomy remain firmly in your hands.
References
- Australian Signals Directorate. ASD’s Blueprint for Secure Cloud. https://blueprint.asd.gov.au/ ↩︎
- Emutare. (2025). Security Technology Stack for Growing Businesses. https://insights.emutare.com/security-technology-stack-for-growing-businesses/ ↩︎
- Fortune Business Insights. (2026). Sovereign Cloud Market Size, Share & Industry Analysis, By Enterprise Type (SMEs and Large Enterprises), By Application (Data Sovereignty, Operational Sovereignty, and Digital Sovereignty), By Industry (BFSI, Healthcare, Government & Public Sector, Manufacturing, and Others), and Regional Forecast, 2026 – 2034. https://www.fortunebusinessinsights.com/sovereign-cloud-market-112386# ↩︎
- Emutare. (2025). Risk-Based Vulnerability Prioritization: A Strategic Approach to Modern Cybersecurity. https://insights.emutare.com/risk-based-vulnerability-prioritization-a-strategic-approach-to-modern-cybersecurity/ ↩︎
- Misra, S., Barik, K., & Kvalvik, P. (2025). Digital sovereignty in the era of Industry 5.0: Challenges and opportunities. Procedia Computer Science, 254, 108–117. https://doi.org/10.1016/j.procs.2025.02.069 ↩︎
- Emutare. (2025). Directory Services Security: Active Directory and Beyond. https://insights.emutare.com/directory-services-security-active-directory-and-beyond/ ↩︎
Related Blog Posts
- Board Reporting on Cybersecurity: What Executives Need to Know
- Multi-Factor Authentication: Comparing Different Methods
- Secrets Management in DevOps Environments: Securing the Modern Software Development Lifecycle
- Zero Trust for Remote Work: Practical Implementation
- DevSecOps for Cloud: Integrating Security into CI/CD
- Customer Identity and Access Management (CIAM): The Competitive Edge for Australian Businesses
- Infrastructure as Code Security Testing: Securing the Foundation of Modern IT

