The concept of “Cyber Defense” is increasingly being viewed as a relic of a slower, less complex era. For decades, the industry has relied on a reactive model: wait for an anomaly, trigger an alert, and hope a human analyst can intervene before the damage spreads. However, in 2026, the speed of automated, AI-driven attacks has rendered human-dependent response times obsolete. To survive, the modern enterprise must move toward “Digital Immunity.”
A Digital Immune System (DIS) combines practices and technologies from software design, development, operations, and analytics to create a self-healing environment. Much like the human biological immune system, a DIS does not just wait for a known virus to enter; it constantly monitors for deviations from “health” and autonomously remediates issues before they manifest as system failures. This shift from manual defense to autonomous immunity is the next great frontier for business resilience.
The Biological Blueprint for Enterprise Security
To understand Digital Immunity, we must look at the transition from traditional perimeter security to identity-based controls. As previously covered in our guide on Implementing Single Sign-On: Pros, Cons, and Best Practices,1 identity is the foundation of modern access. But while SSO tells you who is entering, it does not necessarily ensure that the system they are entering is healthy or capable of defending itself if that user’s credentials have been compromised.
A Digital Immune System creates a layer of “autonomic” security. According to theWorld Economic Forum’s Global Cybersecurity Outlook 2026,2 the most resilient organizations are those that have moved away from “static defense” toward “dynamic adaptability.” This involves integrating observability, artificial intelligence, and automated site reliability engineering (SRE) to create a system that can essentially perform its own surgery while remaining online.
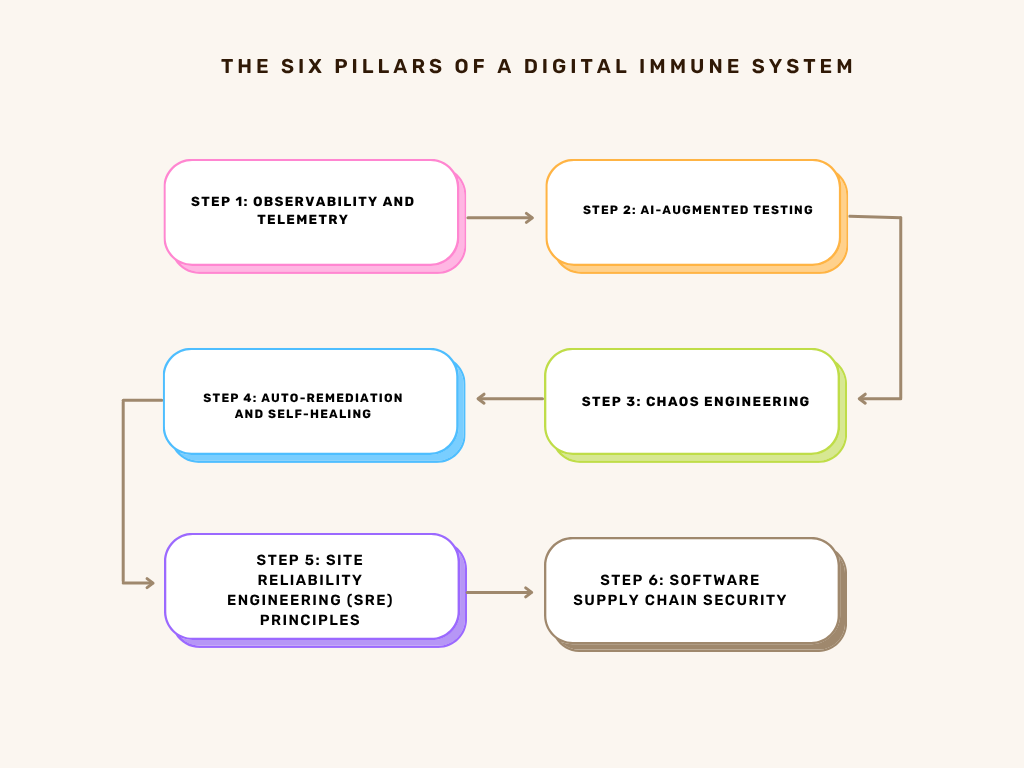
The Six Pillars of a Digital Immune System
Building a self-healing system requires more than just a new piece of software; it requires a modular architecture where every component is designed to fail safely and recover instantly.
1. Observability and Telemetry
You cannot heal what you cannot see. Traditional monitoring tells you if a server is up or down; observability tells you why it is behaving a certain way. By ingesting massive streams of data from applications, networks, and user behaviors, a DIS identifies “pre-failure” states. This level of insight is critical for executive decision-making. As we highlighted in our discussion on Board Reporting on Cybersecurity: What Executives Need to Know,3 the board is increasingly interested in “systemic health” metrics rather than just a list of blocked malware.
2. AI-Augmented Testing
In a Digital Immune System, testing is not a phase that happens before deployment; it is a continuous process. AI-driven testing tools constantly probe the environment for weaknesses, mimicking the way an immune system “learns” from exposure to mild pathogens. This ensures that the system is hardened against real-world conditions long before an actual attacker arrives.
3. Chaos Engineering
In its latest strategic outlook, Cisco’s 2025 Annual Report4 identifies Digital Resilience as a foundational layer for the “AI Era.” The report emphasizes that as autonomous agents and agentic AI become standard, the demand for “intelligent and secure networks” necessitates a shift from reactive security to proactive, fabric-embedded resilience. Cisco highlights that their new security architectures (like Hypershield) are designed to bake this resilience directly into the network fabric to handle unforeseen technical debt and “Agentic AI” demands
4. Auto-Remediation and Self-Healing
This is the core of the immune response. If the observability layer detects a database injection attempt or a memory leak, the DIS does not just send an alert to a human. It takes immediate, scripted action: isolating the affected container, rolling back to the last known “clean” state, or dynamically re-routing traffic.
5. Site Reliability Engineering (SRE) Principles
Digital immunity borrows heavily from the world of SRE, focusing on “error budgets” and automated recovery. The goal is to maximize the “Mean Time Between Failures” (MTBF) while minimizing the “Mean Time to Repair” (MTTR). In 2026, these metrics are the true indicators of a company’s technical maturity.
6. Software Supply Chain Security
Microsoft’s Digital Defense Report 20255 identifies a critical surge in attacks targeting third-party IT management tools and software dependencies. The research highlights a “patching gap” where organizations fail to apply the same rigorous monitoring and update standards to external code as they do for internal systems. This oversight allows attackers to exploit known flaws in trusted third-party software to gain long-term persistence within otherwise secure networks.
Immunity as a Defense Against Ransomware
One of the most powerful applications of Digital Immunity is in the fight against ransomware. Traditional defenses often fail because ransomware moves faster than human response teams can react. However, a self-healing system can detect the rapid file encryption patterns typical of ransomware and instantly “shutter” the data environment.
To learn more about the final line of defense in these scenarios, it is helpful to revisit our insights on Backup and Recovery: Building Resilience Against Ransomware.6 A Digital Immune System enhances this by making the recovery process autonomous. Instead of a manual restoration process that takes days, a self-healing system can identify the exact moment of infection and automatically begin restoring data from immutable backups, often before the IT team is even fully aware of the breach.
The Business Value of Autonomous Resilience
For the C-Suite, the move toward Digital Immunity is a financial decision as much as a technical one. The cost of downtime in 2026 has reached historic highs, with a single hour of operational paralysis costing major enterprises millions in lost revenue and regulatory fines.
By investing in self-healing systems, organizations are essentially buying “uptime insurance.” Research in Cybersecurity Mesh Architecture: A Framework for Enhanced Compatibility and Security in the Digital Age7 indicates that companies utilizing DIS principles experience 80 percent less downtime compared to those relying on traditional SOC (Security Operations Center) models. Furthermore, Digital Immunity allows human analysts to stop doing “toil”—the repetitive, manual tasks of patching and restarting—and focus on high-value strategic initiatives.
Navigating the Implementation Challenges
Transitioning to a Digital Immune System is not without its hurdles. It requires a significant cultural shift from a “blame-oriented” culture to a “learning-oriented” one. Organizations must be willing to accept that failures will happen and focus instead on the speed of recovery.
The Data Overload Problem:
A DIS generates a staggering amount of telemetry. Without advanced AI to filter this data, organizations risk being buried in “false positives.” The key is to start small: pick a single mission-critical application and build an “immune layer” around it before scaling the architecture across the entire enterprise.
The Skills Gap:
Building self-healing systems requires a unique blend of security expertise and software engineering skills. These “DevSecOps” professionals are in high demand in 2026, and organizations may need to invest heavily in upskilling their current workforce to manage the complexities of autonomous security.
Practical Steps for Building Digital Immunity
For leaders ready to begin the pivot toward autonomous resilience, we recommend a phased approach:
- Map Your Critical Pathways: Identify the business processes that must never go down. These are the areas where you should first implement observability and auto-remediation.
- Integrate Security into the CI/CD Pipeline: Ensure that every piece of code is automatically tested for vulnerabilities and “immune compatibility” before it ever reaches production.
- Implement Automated Incident Response: Start by automating simple tasks, such as blocking an IP address after a failed login attempt or restarting a non-responsive microservice.
- Embrace Chaos Testing: Once your basic automations are in place, start challenging them. Run “Game Day” exercises where you simulate a major component failure to see if your system heals itself as expected.
The Future of the Self-Healing Enterprise
As we look toward the end of the decade, the concept of a “security analyst” may transform entirely. Instead of “monitoring the glass” for threats, these professionals will become “immune system architects,” designing the rules and algorithms that allow the company’s digital infrastructure to defend itself.
The end goal is a “Zero-Touch” security environment where the vast majority of threats are identified, isolated, and remediated by the system itself. In this future, cybersecurity is no longer a separate department that “checks” the work of IT; it is an intrinsic quality of the software itself. It is the difference between a building with a security guard and a building that is physically incapable of burning down.
Conclusion: The New Standard of Excellence
Digital Immunity represents the pinnacle of operational resilience. It acknowledges the reality that in an interconnected, AI-driven world, perfection is impossible but survival is mandatory. By building systems that can sense, learn, and heal, business leaders are doing more than just protecting their data; they are ensuring the longevity of their entire corporate legacy.
The journey from defense to immunity is a journey from fear to confidence. When you know your systems can heal themselves, you can innovate faster, take bigger risks, and compete more aggressively. In 2026, resilience is not just about keeping the lights on; it is about having the most robust “biological” advantage in a digital world.
Ready to evolve from reactive defense to true digital immunity? Emutare provides the strategic expertise and technical services needed to build autonomous resilience. From implementing secure Single Sign-On and robust backup strategies to crafting executive board reports on systemic health, we bridge the gap between complex security and business value. Our team helps you master observability, automate remediation, and secure your software supply chain. Don’t just defend your enterprise. Build a self-healing environment that thrives under pressure. Visit our insights portal today to start your journey toward a zero-touch, resilient future.
References
- Emutare. (2025). Implementing Single Sign-On: Pros, Cons, and Best Practices. https://insights.emutare.com/implementing-single-sign-on-pros-cons-and-best-practices/ ↩︎
- World Economic Forum. (2026). Global Cybersecurity Outlook 2026. https://www.weforum.org/publications/global-cybersecurity-outlook-2026/ ↩︎
- Emutare. (2025). Board Reporting on Cybersecurity: What Executives Need to Know. https://insights.emutare.com/board-reporting-on-cybersecurity-what-executives-need-to-know/ ↩︎
- Cisco. (2025). 2025 Annual Report. https://www.cisco.com/c/dam/en_us/about/annual-report/2025-cisco-full-annual-report.pdf ↩︎
- Microsoft. (2025). Microsoft Digital Defense Report 2025. https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/msc/documents/presentations/CSR/Microsoft-Digital-Defense-Report-2025.pdf ↩︎
- Emutare. (2025). Backup and Recovery: Building Resilience Against Ransomware. https://insights.emutare.com/backup-and-recovery-building-resilience-against-ransomware/ ↩︎
- Mampilly, A.J., Midhunchakkaravarthy, D. (2025). Cybersecurity Mesh Architecture: A Framework for Enhanced Compatibility and Security in the Digital Age. In: Pon Selvan, C., Sehgal, N., Ruhela, S., Rizvi, N.U. (eds) International Conference on Innovation, Sustainability, and Applied Sciences. ICISAS 2023. Signals and Communication Technology. Springer, Cham. https://doi.org/10.1007/978-3-031-68952-9_58 ↩︎
Related Blog Posts
- GDPR Compliance for Australian Companies with EU Customers: A Comprehensive Guide for 2025
- Developing Cyber Threat Intelligence Requirements: A Strategic Framework for Modern Organizations
- Cybersecurity Insurance for Australian SMBs: A Critical Shield Against Rising Cyber Threats
- Securing Data Pipelines for AI Training: A Comprehensive Guide for Australian Enterprises
- Hash Functions and Their Applications in Security
- PCI DSS: Implementation Guide for Australian Merchants
- Managed Security Services: When to Outsource

