The traditional concept of the corporate network has effectively dissolved. As we navigate the complexities of 2026, the average enterprise now operates across a fragmented landscape of multi-cloud environments, decentralized remote teams, and an exploding ecosystem of autonomous AI agents. For the modern Chief Information Officer (CIO) or Chief Information Security Officer (CISO), the challenge is no longer about defending a single fortress. Instead, it is about securing a distributed nation of assets that exist everywhere and nowhere at once.
The “castle and moat” strategy, which relied on a strong perimeter to keep threats out, has been rendered obsolete by the sheer velocity of digital transformation. Today, data is the lifeblood of the organization, and that data flows through third-party APIs, home offices, and public cloud instances. To protect this flow, leaders are turning to a more fluid, modular approach: Cybersecurity Mesh Architecture (CSMA). Originally proposed as a conceptual framework by analysts, CSMA has matured into the operational standard for organizations that prioritize agility without sacrificing integrity. By 2026, the adoption of mesh-based solutions has become a competitive differentiator, driven by a desperate need for interoperability in an era where the average enterprise manages an overwhelming number of distinct, disconnected security tools.
The Death of the Castle and Moat
For decades, security was perimeter-centric. We built high walls (firewalls) and deep moats (VPNs) around our data centers. However, as we move into a world where over 60 percent of enterprise workloads reside in the cloud, that perimeter has become a sieve. To learn more about the initial shifts away from traditional boundaries and how they impact modern access, it is helpful to review our previous analysis on Implementing Single Sign-On: Pros, Cons, and Best Practices.1 SSO was the first step in recognizing that identity, not the physical network, is the true perimeter.
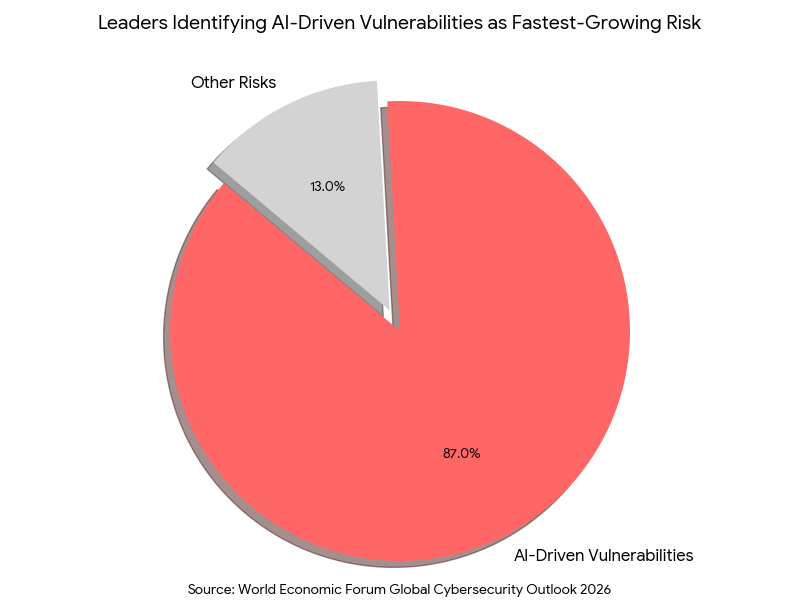
CSMA takes this a step further. Instead of one big wall, it creates a flexible, modular “mesh” of security controls around every individual user, device, and digital asset. This shift is critical because, according to the World Economic Forum’s Global Cybersecurity Outlook 2026,2 a staggering 87 percent of leaders now identify AI-driven vulnerabilities as their fastest-growing risk. In such a high-velocity threat environment, a static perimeter is nothing more than a stationary target. A distributed mesh, by contrast, is a resilient ecosystem capable of absorbing shocks and isolating compromises before they become catastrophic.
The Architectural Shift: Why Mesh, Why Now?
The transition to CSMA is not merely a technical upgrade; it is a response to the “security sprawl” that has plagued IT departments for years. Most organizations have inadvertently built a “Frankenstein’s Monster” of security: a collection of best-of-breed tools that do not speak the same language. When a threat is detected by an endpoint tool, it often takes minutes or even hours for that information to reach the firewall or the identity provider. In the world of 2026, where automated attacks occur at millisecond speeds, this delay is fatal.
CSMA solves this by creating an interoperable layer where security tools can share intelligence and coordinate a response. It shifts the focus from “protection at the edge” to “protection at the point of access.” This is why identity has become the central pillar of the mesh. As previously covered in our guide on Board Reporting on Cybersecurity: What Executives Need to Know,3 identity is the most significant risk factor for modern boards. A mesh architecture ensures that identity verification (utilizing adaptive MFA and decentralized directory services) follows the user regardless of whether they are in a coffee shop, a corporate office, or a satellite branch.
The Four Pillars of a Functional Mesh
Implementing a mesh architecture is not about buying a single product. It is a design philosophy built on four foundational layers that allow disparate security tools to work as a unified system. Understanding these pillars is essential for any IT professional tasked with modernizing a legacy environment.
1. Security Analytics and Intelligence
This layer acts as the “brain” of the mesh. It ingests telemetry from every corner of the enterprise, from a developer’s laptop in London to a serverless function in a cloud instance, to identify patterns that a siloed tool would inevitably miss. In 2026, this layer is increasingly powered by agentic AI, which can correlate millions of events in real-time to spot the subtle markers of a sophisticated breach.
2. Distributed Identity Fabric
The identity fabric is the “glue” that binds the mesh together. It ensures that a user’s permissions are consistent across all platforms. This layer is what allows for “Continuous Authentication,” where the system doesn’t just check a password at login but monitors behavioral signals (like typing speed or mouse movement) to ensure the session hasn’t been hijacked. Verizon’s 2025 Data Breach Investigations Report4 confirms that stolen credentials remain the primary attack vector, involved in 88 percent of web application breaches. This data highlights the urgent need for a continuous identity fabric to detect the rising wave of session hijacking and sophisticated multi-factor authentication bypass techniques.
3. Consolidated Policy Management
In a traditional setup, a security admin might have to update a policy in five different consoles to block a specific type of traffic. In a CSMA framework, policies are “composable.” You write the rule once (for example, “no unmanaged device can access the financial database”) and the mesh enforces it across the cloud, the network, and the endpoint. This level of orchestration is what separates a modern enterprise from a legacy one.
4. Integrated Dashboards and Orchestration
The final pillar is the “single pane of glass.” Security teams are tired of “swivel-chair” management. CSMA provides a unified view of the entire security posture. This visibility is essential for resilience. As we explored in our deep dive intoBackup and Recovery: Building Resilience Against Ransomware,5 recovery is the final line of defense. However, a mesh architecture allows for “micro-segmentation,” meaning that if a single node is hit by ransomware, the mesh can automatically isolate that node, preventing the lateral movement that leads to a total company-wide lockout.
The Role of Interoperability in 2026
One of the greatest hurdles to security in the past was vendor lock-in. Companies were forced to buy everything from one provider just to ensure the tools worked together. CSMA breaks this cycle. It is built on the principle of “Open APIs” and standardized data formats. This means that a business can choose the best firewall, the best endpoint protection, and the best cloud security tool, and they will all function as a cohesive unit.
This interoperability is not just a convenience; it is a requirement for modern compliance. Recent research Cybersecurity Mesh Architecture: A Framework for Enhanced Compatibility and Security in the Digital Age,6 highlights that decentralized architectures are the only viable way to protect “cyber-physical systems.” These are the sensors, smart devices, and IoT hardware that power modern manufacturing and infrastructure. Without a mesh, these devices often represent unmonitored backdoors into the corporate core, as they are often too low-powered to run traditional security agents.
Enhancing Operational Resilience
The conversation around cybersecurity has shifted from “preventing an attack” to “ensuring continuity.” This is where CSMA truly shines. Because the security controls are distributed, there is no single point of failure. If one part of the security mesh is compromised or goes offline, the rest of the mesh continues to protect the remaining assets.
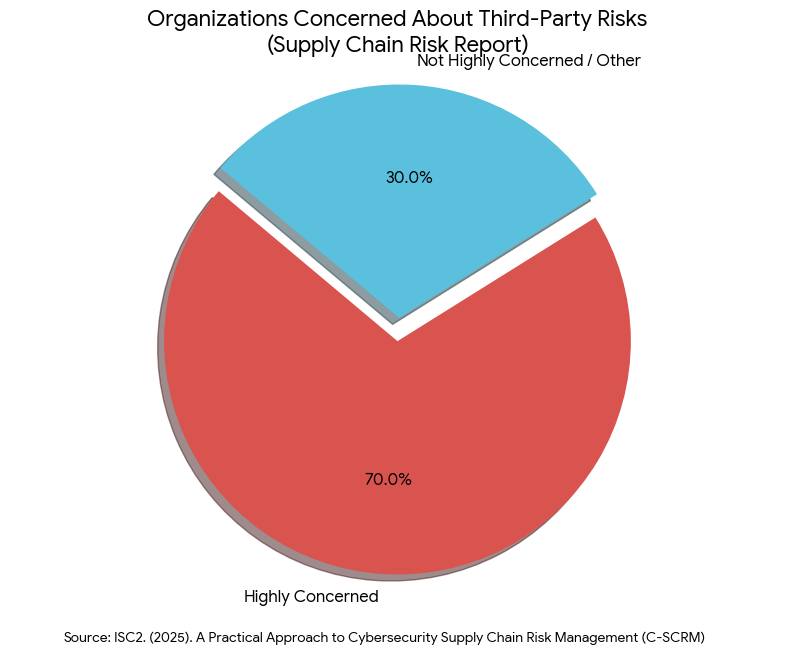
This “self-healing” capability is essential for managing the supply chain risks that have become so prevalent. A recent2026 Supply Chain Risk Report7 from ISC2 notes that 70 percent of organizations are now highly concerned about third-party risks. By treating every third-party connection as an individual “node” in the mesh, businesses can grant granular access and immediately revoke it if the partner’s security is compromised, without affecting the rest of the operation.
The Human Element: Reducing Security Fatigue
An often-overlooked benefit of CSMA is its impact on the workforce. Traditional security measures are often “high-friction,” requiring users to jump through multiple hoops to get their work done. This leads to “security fatigue,” where employees look for workarounds (like using personal cloud storage) just to stay productive.
By utilizing an identity fabric and adaptive authentication, CSMA makes security nearly invisible to the end-user. If a user is on a known device, in a known location, performing a routine task, the mesh stays in the background. If the user suddenly attempts to download 50 gigabytes of data from an unrecognized IP address, the mesh steps in to challenge them. This “just-in-time” security reduces friction and increases compliance across the board.
Practical Implementation: A Roadmap for Leaders
Transitioning to a mesh architecture is an iterative process. It does not require a “rip and replace” of your existing stack. Instead, follow this tactical roadmap:
- Audit Your Identity Lifecycle: Before you can build a mesh, you must have a clean directory. Ensure you have a process for off-boarding both employees and “ghost” service accounts. If an identity hasn’t been used in 30 days, the mesh should be able to disable it automatically.
- Prioritize API-First Tools: When selecting new vendors, make interoperability a non-negotiable requirement. A tool that cannot share telemetry with your broader ecosystem is a liability.
- Move Policy to the Center: Start migrating your security rules from individual devices to a central policy engine. This allows for the “write once, enforce everywhere” capability that defines CSMA.
- Focus on Visibility: Invest in a platform that can aggregate data from your entire distributed enterprise. You cannot protect what you cannot see, and you cannot orchestrate what you haven’t mapped.
Conclusion: From Defense to Durability
As we look toward the remainder of 2026 and beyond, the goal of cybersecurity is no longer just “protection.” It is “durability.” The Cybersecurity Mesh Architecture represents the ultimate evolution of the Zero Trust philosophy. It acknowledges that in a distributed world, we cannot trust the network, the device, or even the physical location. We can only trust the identity of the actor and the context of the interaction.
By moving toward a mesh, organizations stop playing a perpetual game of “Whac-A-Mole” with threats and start building a system that is inherently resilient. The enterprises that thrive in this era will not be those that never get attacked, but those that have built a mesh flexible enough to absorb the blow, isolate the damage, and keep the business running without missing a beat. This is the new standard of excellence for the distributed enterprise.
Secure your distributed enterprise with Emutare. Our expert consultants help you transition from legacy perimeters to a resilient Cybersecurity Mesh Architecture. We specialize in deploying continuous identity fabrics and adaptive MFA to eliminate credential-based risks. Emutare streamlines your security sprawl by integrating disparate tools into a unified, interoperable ecosystem. From auditing your identity lifecycle to implementing automated ransomware isolation, we ensure your business remains durable against evolving AI threats.
References
- Emutare. (2025). Implementing Single Sign-On: Pros, Cons, and Best Practices. https://insights.emutare.com/implementing-single-sign-on-pros-cons-and-best-practices/ ↩︎
- World Economic Forum. (2026). Global Cybersecurity Outlook 2026. https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf ↩︎
- Emutare. (2025). Board Reporting on Cybersecurity: What Executives Need to Know. https://insights.emutare.com/board-reporting-on-cybersecurity-what-executives-need-to-know/ ↩︎
- Verizon. (2025). 2025 Data Breach Investigations Report. https://its.ny.gov/system/files/documents/2025/06/maguire-verizon.pdf? ↩︎
- Emutare. (2025). Backup and Recovery: Building Resilience Against Ransomware. https://insights.emutare.com/backup-and-recovery-building-resilience-against-ransomware/ ↩︎
- Mampilly, A. J., & Midhunchakkaravarthy, D. (2025). Cybersecurity mesh architecture: A framework for enhanced compatibility and security in the digital age. In International Conference on Innovation, Sustainability, and Applied Sciences (pp. 441–445). https://www.springerprofessional.de/en/cybersecurity-mesh-architecture-a-framework-for-enhanced-compati/50633028 ↩︎
- ISC2. (2025). A Practical Approach to Cybersecurity Supply Chain Risk Management (C-SCRM). https://www.isc2.org/Insights/2025/12/a-practical-guide-to-supply-chain-risk-management ↩︎
Related Blog Posts
- Cybersecurity Essentials for Startups: Safeguarding Your Business from Digital Threats
- Insider Threats: Detection and Prevention Strategies
- Securing Microsoft 365 Email Environments: A Comprehensive Guide
- Crisis Communication During Security Incidents: A Strategic Approach
- Building a Security Operations Center (SOC): Key Components
- Implementing Single Sign-On: Pros, Cons, and Best Practices
- Backup and Recovery: Building Resilience Against Ransomware

