The digital landscape of 2026 has been fundamentally reshaped by a new global reality: the inseparable link between geotechnology, geoeconomics, and national security. We have moved past the era of the “borderless internet” into an age where code has a nationality and data has a home. Countries are no longer content to simply host their data on global public clouds; they are increasingly demanding “Digital Sovereignty,” the ability to maintain full operational and legal control over their technological destinies.
This shift has given rise to the Sovereign Cloud, a localized infrastructure model designed to meet the specific legal and security requirements of a single jurisdiction. For global enterprises, this means the end of unified, monolithic cloud architectures. Navigating the geopolitics of code requires a sophisticated understanding of data residency laws, cross-border transfer restrictions, and the emerging “fragmentation” of the global software supply chain. This article explores how business leaders can adapt to this balkanized digital world without sacrificing the scalability and innovation that cloud computing provides.
The Rise of Sovereign Cloud in a Fractured World
Escalating geopolitical tensions and a desire for technological independence are driving a massive surge in sovereign cloud investment. The New Cloud Policy: Accelerating secure, modern government services1 policy framework from the Australian Government mandates secure, resilient, and strategically planned cloud adoption across the Australian Public Service. It embeds cloud expenditure management, security, and governance, signalling substantial public cloud investment direction and sovereign cloud considerations for government digital transformation in 2026 onward.
This is not merely a regulatory trend; it is a strategic repositioning as nations seek to protect “wealth generation” within their own borders and shield critical infrastructure from foreign interference.
To learn more about how this trend aligns with broader security strategies, Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM)2 highlights that “exposure” is now a geographic concern. If your data resides in a jurisdiction with weak legal protections or high geopolitical risk, that asset is fundamentally exposed, regardless of your technical encryption.
Business leaders are feeling this pressure acutely. The Take control of your digital future with Google Sovereign3 from Google discusses customer concerns about foreign government access to data stored in the cloud and explains how sovereign cloud solutions and local partnerships help address those concerns by giving customers more local control and compliance options. It directly ties geopolitical risk to cloud workload deployment decisions.
Operationalizing Trust in a “Balkanized” Data Landscape
As data residency laws become more prescriptive, the “Feedback Loop” between global headquarters and local subsidiaries is often the first thing to break. When a country mandates that data cannot leave its borders even for security analysis, the traditional centralized Security Operations Center (SOC) becomes non-compliant.
As previously covered in Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs,4 trust is broken when global policies fail to account for local realities. In a sovereign cloud environment, organizations must move toward “Federated Security Models,” where data is processed locally, and only high-level, anonymized insights are shared centrally. This preserves compliance while maintaining a unified defense posture.
This challenge is echoed in Microsoft’s Announcing comprehensive sovereign solutions empowering European organizations5 an overview of expanded sovereign cloud capabilities, including customer-controlled encryption and key management to support data sovereignty objectives. This shows how encryption and control matter to sovereignty. By maintaining control of the encryption keys, organizations can achieve a form of “Logical Sovereignty,” ensuring that even if data is physically stored in a foreign cloud, it remains inaccessible to unauthorized third parties or foreign governments.
The API Border Control: Governing Cross-Border Flows
APIs are the primary vehicles for cross-border data transfers, yet they are often the least-governed part of the sovereign cloud strategy. A single API call from a mobile app in Europe to a database in the United States can trigger a violation of the EU AI Act or local data residency laws if sensitive information is included in the payload.
Effective API Asset Governance: Identifying and Decommissioning Obsolete Endpoints6 must now include a “Geographic Audit.” Governance teams need to map exactly where every API endpoint resides and where the data it touches originates. If an “obsolete” endpoint is still transmitting data across restricted borders, it represents a massive compliance liability that could lead to fines reaching 7% of global turnover under the newest regulations.
The complexity of this task is growing as many enterprises now uses many APIs, making manual tracking impossible. Without automated governance that understands the “nationality” of a data packet, organizations are effectively flying blind through a geopolitical storm.
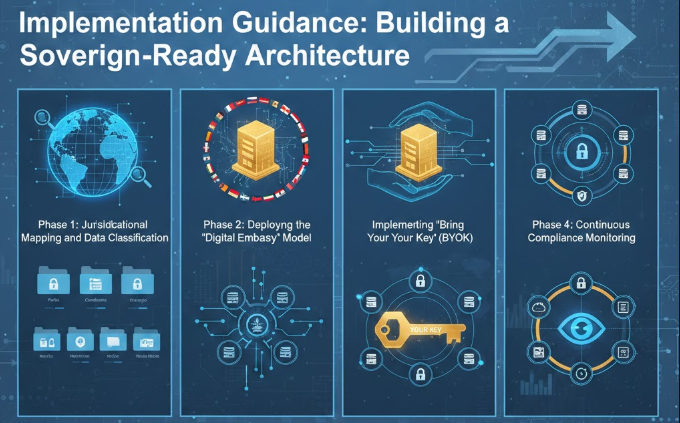
Implementation Guidance: Building a Sovereign-Ready Architecture
Navigating the geopolitics of code requires a multi-layered approach that combines legal strategy with technical “data-centric” security.
Phase 1: Jurisdictional Mapping and Data Classification
You cannot protect what you cannot locate.
- Map Data Lineage: Identify where your data is born, where it is processed, and where it is stored.
- Classify by Sovereignty Risk: Categorize data based on local laws (e.g., “Sovereign Only” for national security data vs. “Global” for public marketing materials).
- Audit “Shadow Residency”: Use automated tools to find data stored in unauthorized regions by employees or autonomous AI agents.
Phase 2: Deploying the “Digital Embassy” Model
To balance global scale with local sovereignty, organizations are adopting “Digital Embassy” architectures, secure, localized compute enclaves.
- Localized Compute: Deploy sensitive AI workloads on sovereign cloud providers like the AWS European Sovereign Cloud7 or IBM Sovereign Core.
- Edge Governance: Process as much data as possible at the “edge” within the host country, sending only non-sensitive metadata to global hubs.
Phase 3: Implementing “Bring Your Own Key” (BYOK)
The ultimate proof of sovereignty is the control of the “Kill-Switch.”
- Centralized Key Management: Use an external Key Management System (KMS) that you control, separate from the cloud provider’s infrastructure.
- Zero-Trust Transfer: Ensure that any data crossing a border is encrypted at rest and in transit, with keys that never leave the country of origin.
Phase 4: Continuous Compliance Monitoring
In 2026, compliance is not a point-in-time audit; it is a real-time stream.
- Automated Transfer Impact Assessments (TIAs): Use AI to continuously monitor cross-border data flows and automatically block transfers that violate updated local laws.
- Residency Alerts: Set up automated triggers in your SOC to alert teams whenever an asset “moves” into a high-risk or non-compliant geographic zone.
Conclusion
The era of the “Global Cloud” is being replaced by the “Interoperable Sovereign Cloud.” In this new landscape, the ability to navigate the geopolitics of code is a core business competency. Organizations that continue to ignore the “nationality” of their digital assets will find themselves facing not just technical breaches, but the much more severe risks of regulatory shutdown and geopolitical de-platforming.
By embracing a strategy that combines Continuous Threat Exposure Management (CTEM), operational trust, and rigorous API governance, business leaders can turn the challenge of digital sovereignty into a competitive advantage. The goal is no longer to build a single global network, but to build a resilient, “Sovereign-Ready” enterprise that can thrive in a fragmented, complex, and fascinatingly diverse world.
In a world where data has a nationality, Emutare empowers your organization to navigate the complexities of digital sovereignty. We provide expert cybersecurity governance and consultation to align your global operations with local residency laws. Our team specializes in implementing advanced security controls, SIEM, and XDR deployment to support federated security models and maintain a unified defense. From jurisdictional risk assessments to technical architecture development, Emutare ensures your enterprise remains compliant, resilient, and secure across every border.
References
- Australian Government Digital Transformation Agency. (2025). New Cloud Policy: Accelerating secure, modern government services. https://www.dta.gov.au/media-releases/new-cloud-policy-accelerating-secure-modern-government-services? ↩︎
- Emutare. (2026). Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM). https://insights.emutare.com/stop-patching-everything-the-case-for-continuous-threat-exposure-management-ctem/ ↩︎
- Google. (2025). Take control of your digital future with Google Sovereign. https://services.google.com/fh/files/misc/google_sovereign_cloud_whitepaper_jan_2025.pdf? ↩︎
- Emutare. (2026). Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs. https://insights.emutare.com/operationalizing-trust-fixing-the-broken-feedback-loop-in-modern-socs/ ↩︎
- Microsoft. (2025). Announcing comprehensive sovereign solutions empowering European organizations. https://blogs.microsoft.com/blog/2025/06/16/announcing-comprehensive-sovereign-solutions-empowering-european-organizations/ ↩︎
- Emutare. (2026). API Asset Governance: Identifying and Decommissioning Obsolete Endpoints. https://insights.emutare.com/api-asset-governance-identifying-and-decommissioning-obsolete-endpoints/ ↩︎
- AWS. (2025). AWS European Sovereign Cloud. https://aws.eu/ ↩︎
Related Blog Posts
- GDPR Compliance for Australian Companies with EU Customers: A Comprehensive Guide for 2025
- Developing Cyber Threat Intelligence Requirements: A Strategic Framework for Modern Organizations
- Cybersecurity Insurance for Australian SMBs: A Critical Shield Against Rising Cyber Threats
- Securing Data Pipelines for AI Training: A Comprehensive Guide for Australian Enterprises
- Hash Functions and Their Applications in Security
- PCI DSS: Implementation Guide for Australian Merchants
- Managed Security Services: When to Outsource

