The relationship between security teams and software developers has historically been one of friction. Security is often viewed as a “tax” on innovation, a series of hurdles designed to slow down the release cycle in the name of safety. However, as we navigate 2026, a fundamental shift is occurring. Leading organizations are moving away from treating security as a centralized enforcement agency and are instead adopting a “Security as a Product” mindset.
This approach applies the core principles of product management, user-centered design, iterative feedback, and roadmap prioritization, to internal security tools and policies. By treating developers as “customers” rather than “subjects,” security teams can build solutions that people actually want to use. This transformation is essential for managing the velocity of modern development, where AI-assisted coding and ephemeral cloud architectures have made manual gatekeeping impossible.
Bridging the Divide: From Enforcement to Enablement
Traditional security models rely on “breaking the build” to enforce compliance, a practice that leads to frustration and “shadow” workarounds. When security is treated as a product, the success metric shifts from “number of vulnerabilities blocked” to “developer adoption and satisfaction.” If a security tool is slow, confusing, or produces high rates of false positives, it is a “bad product” that requires a redesign, not more enforcement.
As previously covered in Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs,1 the foundation of any high-performing security organization is a functional feedback loop. In a product-centric model, this loop is formalized. Security teams conduct user interviews with developers, track the “Net Promoter Score” (NPS) of their security scanners, and prioritize the “user experience” of remediation workflows.
The impact of this shift is measurable. According to research from Google’s 2025 DORA State of AI-assisted Software Development Report2 on AI-Assisted Software Development, while 90% of developers have embraced AI to accelerate coding, 30% of teams report that manual or disconnected security processes remain a critical bottleneck that negates these speed gains.
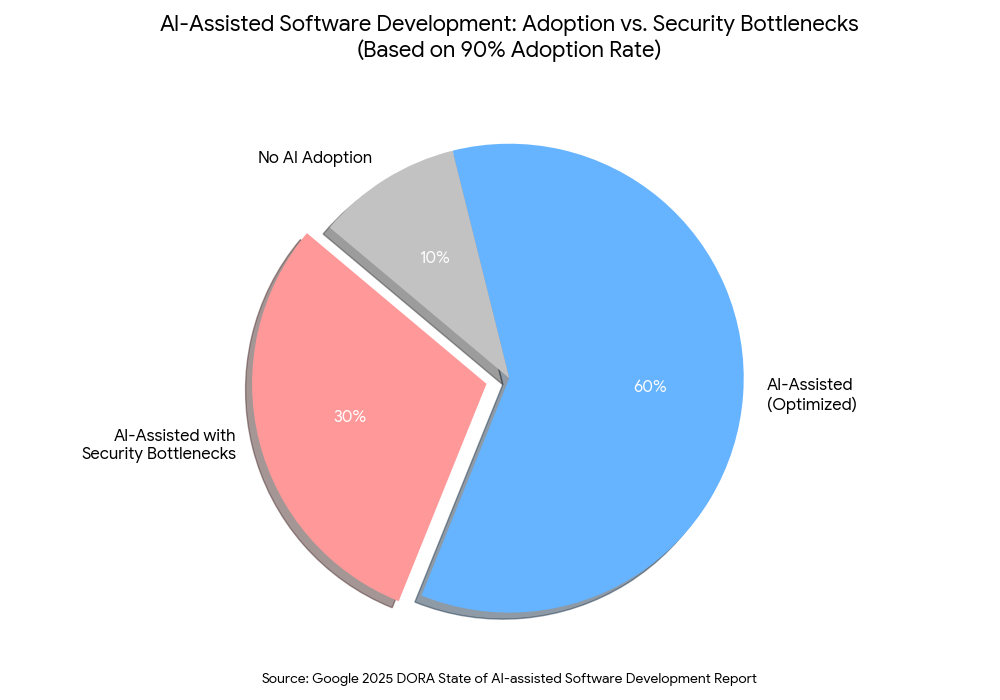
The findings highlight a growing “AI Paradox” where the surge in code volume has increased delivery instability, as traditional security and testing frameworks struggle to keep pace with AI-driven velocity. Consequently, teams operating with manual security gates experience significantly higher levels of burnout and friction compared to those utilizing automated foundations.
Organizations that treat security as a product see significantly lower friction because security controls are integrated directly into the tools developers already use, such as their IDEs and CI/CD pipelines, rather than being managed in a separate, siloed dashboard.
The Rise of the Cybersecurity Product Manager
A key indicator of this trend is the emergence of a new hybrid role: the Cybersecurity Product Manager (PM). Unlike a security engineer who focuses on the “how” of a technical control, the Cybersecurity PM focuses on the “why” and the “who.” They are responsible for defining a security roadmap that aligns with business goals while minimizing impact on engineering velocity.
Microsoft’s 2026 outlook emphasizes that PMs are now responsible for the automated synchronization of regulatory signals (like NIS2 and GDPR) into product backlogs. According to Microsoft’s curriculum for AI Product Managers, Build and manage assessments in Compliance Manager,3 the role now requires specific proficiency in security and compliance strategies to ensure that products, especially those utilizing agentic AI, are launched with active “guardrail layers” rather than theoretical guidelines. They treat a security requirement not as a mandate, but as a feature request. By balancing innovation with protective controls, they ensure that the path of least resistance for a developer is also the most secure path.
This role is particularly vital when managing the “Great Convergence” of security tools. To learn more about how fragmented tools can be unified into a cohesive experience,Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM)4 explains how moving toward a context-aware exposure management platform allows teams to focus on the risks that actually matter, effectively “pruning” the product backlog of low-value security noise.
Reducing “Verification Debt” in the AI Era
In 2026, the volume of code being produced is staggering, thanks to Agentic AI and automated code generation. This has led to what industry experts call “verification debt,” the gap between the code being created and the ability of security teams to validate it. Treating security as a product is the only way to scale defenses at the speed of AI.
The 2025 Cisco Cybersecurity Readiness Index reveals5 that while 96% of organizations plan to upgrade their infrastructure to combat modern threats, a mere 4% have actually achieved a “Mature” level of security readiness. This “confidence gap” is often due to a lack of context. When security is a product, the “context” is built into the tool. For example, a developer shouldn’t just be told a library is vulnerable; they should be provided with a pre-validated, “safe” version of that library that can be swapped in with a single click.
This level of governance extends to the API layer as well. Effective API Asset Governance: Identifying and Decommissioning Obsolete Endpoints6 requires that the process of decommissioning an endpoint be as simple as the process of creating one. By creating “Self-Service Decommissioning” products, IT teams can reduce the attack surface without requiring manual intervention from a security specialist.
Implementation Guidance: Building the Security Product Roadmap
For business leaders looking to transition to this model, the following phases offer a practical implementation guide.
Phase 1: Empathy and Discovery
Start by understanding your “customers” (the developers).
- Conduct User Research: Shadow developers for a day to see where security tools interrupt their flow.
- Audit the Tooling Friction: Identify which security tools have the highest “time-to-fix” or the highest rate of ignored alerts.
- Identify “Power Users”: Find developers who are already security-conscious and involve them in the design of new security products.
Phase 2: Define the “Minimum Viable Security” (MVS)
Don’t try to build the perfect security suite on day one.
- Focus on High-Impact Friction: If “secrets management” is the biggest pain point, build or buy a product that makes secret injection seamless.
- Establish “Paved Roads”: Create pre-approved, secure templates for common tasks (e.g., deploying a new S3 bucket or a new microservice). If a developer uses the “paved road,” they get an express pass through the security review.
Phase 3: Measure what Matters (Security KPIs)
Move beyond “CVE count” to product-centric metrics.
- Mean Time to Remediation (MTTR): How long does it take for a developer to fix a critical bug once notified?
- Tool Adoption Rate: What percentage of teams are actively using the internal security platform?
- False Positive Rate: If more than 5% of alerts are false positives, the “product” is failing and needs a fix.
Phase 4: Iterate and Evangelize
Security as a Product is a living process, not a destination.
- Release Notes for Security: When you update a security policy or tool, publish “Release Notes” explaining the benefit to the developer (e.g., “This update reduces scan times by 30%”).
- Internal Marketing: Host “Lunch and Learns” to show how the new security products make the developer’s life easier, not harder.
Conclusion
The transition to Security as a Product marks the end of the “siloed” security era. In 2026, the most successful organizations will be those that realize their developers’ time is their most valuable asset. By applying product management discipline to security, we can build a culture where safety is baked into the DNA of the product, not bolted on as an afterthought.
As the threat landscape becomes more automated and complex, the “security product” must become more intuitive and invisible. When we move beyond the prompt and focus on the user experience of security, we don’t just reduce risk, we accelerate the entire business.
Emutare helps your organization transition to a Security as a Product model by bridging the gap between security mandates and developer velocity. Our Cybersecurity Consultation and Advisory services align security roadmaps with your business goals, treating requirements as features rather than hurdles. We streamline workflows through Al Driven Process Automation, Vulnerability Management, and Software Development expertise, ensuring security is integrated directly into your existing tools. Partner with Emutare to build a resilient, compliant digital landscape where the most secure path is also the path of least resistance.
References
- Emutare. (2025). Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs. https://insights.emutare.com/operationalizing-trust-fixing-the-broken-feedback-loop-in-modern-socs/ ↩︎
- Google. (2025). 2025 DORA State of AI-assisted Software Development Report. https://services.google.com/fh/files/misc/2025_state_of_ai_assisted_software_development.pdf ↩︎
- Microsoft. Build and manage assessments in Compliance Manager. https://learn.microsoft.com/en-us/purview/compliance-manager-assessments ↩︎
- Emutare. (2025). Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM). https://insights.emutare.com/stop-patching-everything-the-case-for-continuous-threat-exposure-management-ctem/ ↩︎
- Cisco. (2025). 2025 Cisco Cybersecurity Readiness Index reveals. https://newsroom.cisco.com/c/dam/r/newsroom/en/us/interactive/cybersecurity-readiness-index/2025/documents/2025_Cisco_Cybersecurity_Readiness_Index.pdf ↩︎
- Emutare. (2025). API Asset Governance: Identifying and Decommissioning Obsolete Endpoints. https://insights.emutare.com/api-asset-governance-identifying-and-decommissioning-obsolete-endpoints/ ↩︎
Related Blog Posts
- Cybersecurity Essentials for Startups: Safeguarding Your Business from Digital Threats
- Insider Threats: Detection and Prevention Strategies
- Securing Microsoft 365 Email Environments: A Comprehensive Guide
- Crisis Communication During Security Incidents: A Strategic Approach
- Building a Security Operations Center (SOC): Key Components
- Implementing Single Sign-On: Pros, Cons, and Best Practices
- Backup and Recovery: Building Resilience Against Ransomware

