In the digital ecosystem of 2026, the “SaaS Sprawl” has evolved from a manageable budget line item into a sprawling, multi-headed governance challenge. The average enterprise now relies on more than 110 distinct SaaS applications, a number that continues to climb as departments independently adopt “Agentic AI” tools and niche vertical solutions. While these platforms drive agility, they have also created a massive visibility gap. Today, security and IT leaders are not just managing vendors; they are managing an interconnected web of data permissions, third-party risks, and “Zombie Accounts” that exist entirely outside the corporate perimeter.
The era of “growth at all costs” has been replaced by the era of “Efficient Growth,” where the priority is no longer just adding features, but orchestrating the existing stack for resilience and value. Managing this sprawl requires moving beyond the traditional procurement gatekeeper model toward a philosophy of continuous asset governance. This article examines the systemic risks of unmanaged SaaS ecosystems and provides a strategic roadmap for business leaders to reclaim control without stifling the innovation that cloud-based tools provide.
The Financial and Operational Toll of Uncontrolled Sprawl
SaaS sprawl is a silent drain on the enterprise, manifesting as both financial waste and technical debt. When multiple departments purchase redundant tools, such as three different project management platforms or five separate AI content generators, the organization loses all negotiating leverage. More importantly, it creates “data silos” where information is trapped in unmanaged environments, making it impossible for the business to maintain a single source of truth.
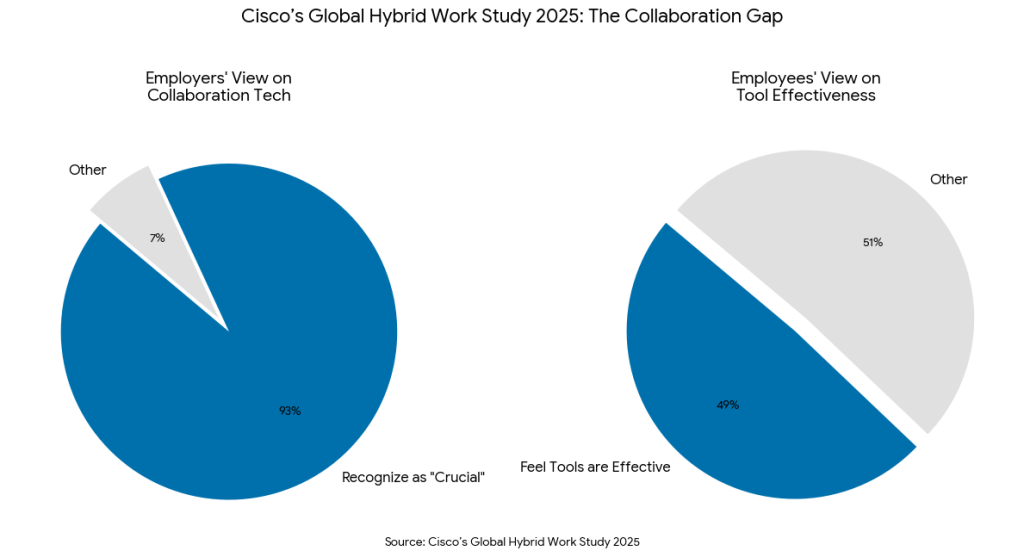
To learn more about the shift from reactive management to a proactive posture, Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM)1 highlights a critical lesson: you cannot protect what you cannot see. In the context of SaaS, this means that every “Shadow IT” application is a blind spot that evades traditional vulnerability scanning. Cisco’s Global Hybrid Work Study 20252 into the modern workplace emphasizes that while 93% of employers recognize collaboration technology as “crucial,” only 49% of employees feel their organization provides consistent, effective tools. This gap often leads to “Shadow IT,” where employees independently purchase SaaS subscriptions to fill the void, creating the non-payroll expense “sprawl” you referenced.
Operationalizing Trust in the Decentralized Stack
The biggest risk of SaaS sprawl is not just the cost, but the breakdown of the “Feedback Loop” between IT and the end-users. When employees find official tools too slow or clunky, they bypass them. This “Shadow IT” is often driven by a desire for efficiency, but it results in sensitive company data being uploaded to unvetted consumer-grade platforms that may use that data to train public AI models.
As previously covered in Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs,3 trust is a two-way street. If the IT department acts only as a “Department of No,” users will continue to seek workarounds. In 2026, the goal is to build a “Privacy by Design” culture where the secure, sanctioned tool is also the easiest to use. Without this operational trust, the SOC is left to play a permanent game of “Whack-a-Mole” with new, unauthorized endpoints.
This operational challenge is compounded by the rise of “Shadow AI.” Research from Google Cloud’s Cybersecurity Forecast 20264 indicates that the expansion of the digital perimeter is being driven by the rise of agentic AI and decentralized technology adoption. This evolution transitions the attack surface from traditional infrastructure to a complex ecosystem of autonomous digital actors. As organizations increasingly deploy AI agents to handle critical workflows, these non-human entities are becoming the primary targets for exploitation, necessitating a shift toward identity centric security models that can manage the fluid nature of modern API and SaaS connections.
API Governance and the “Zombie App” Crisis
A significant portion of SaaS risk resides in “Zombie Applications,” tools that were purchased for a single project, forgotten by the user, but still retain active, authenticated connections to the core company database via APIs. These persistent backdoors are often overlooked because the primary user has left the company, but the service account remains active.
Rigorous API Asset Governance: Identifying and Decommissioning Obsolete Endpoints5 is the only way to close these gaps. Every SaaS integration creates an API endpoint; if that endpoint is not governed and decommissioned after use, it remains a “latent” vulnerability. Attackers in 2026 increasingly target these forgotten integrations because they provide a path of least resistance into the enterprise’s most sensitive data.
Findings from the Google Cloud 2025 ROI of AI Study6 underscore a rapid shift toward autonomous operations, revealing that 52% of executives have already deployed AI agents within their organizations.
As these agents proliferate, the research notes that privacy and security have become the primary concerns for leadership. To manage this expansion effectively, Google emphasizes the necessity of a modern data strategy rooted in strong governance. This approach ensures that as agents are embedded across core business processes, they remain tethered to a clear framework of accountability and integration to prevent the security risks associated with unmanaged growth.
Implementation Guidance: A Strategic Roadmap for SaaS Governance
To master vendor governance in an age of sprawl, business leaders should implement a framework focused on visibility, accountability, and automation.
Phase 1: Total Stack Visibility
Stop relying on expense reports to find SaaS. In 2026, the primary method of discovery should be automated and continuous.
- Implement SSPM: Use SaaS Security Posture Management tools to identify every app connected to your SSO or email environment.
- Inventory API Connections: Map every third-party tool that has “Read/Write” access to your CRM, ERP, or data warehouse.
- Categorize by Risk: Group vendors into tiers (e.g., Tier 1 for those handling PII, Tier 3 for low-risk productivity tools).
Phase 2: Establish “Productivity-First” Policies
Governance should enable work, not block it.
- Self-Service Catalog: Create a centralized marketplace of “IT-Sanctioned” apps. If an employee needs a new tool, they should be able to “One-Click” request it from a pre-vetted list.
- The “Shadow IT” Amnesty: Instead of punishing users for unauthorized apps, provide a path to bring them into the fold if they pass a basic security review.
Phase 3: Automate the Lifecycle
Manual tracking in spreadsheets is the enemy of security.
- Automated Offboarding: Ensure that when an employee leaves, their access is revoked across all SaaS platforms, including those not behind the main SSO.
- Renewal Guardrails: Set automated triggers 90 days before a contract expires to review usage data. If a tool has less than 20% engagement, it should be slated for decommissioning or consolidation.
Phase 4: Continuous Monitoring and “Kill Switches”
Develop an incident response plan specifically for SaaS breaches.
- Integration Audits: Quarterly review of what “permissions” each app has. Revoke permissions that are no longer needed for the tool to function.
- Vendor Breach Readiness: Establish a protocol for what happens if a third-party vendor (like a major CRM or AI provider) is compromised.
Conclusion
The challenge of 2026 is not to stop SaaS adoption, but to govern its sprawl. As the boundaries of the enterprise continue to dissolve into a cloud-native mesh, the traditional “Gatekeeper” role of IT must evolve into an “Orchestrator” role. By applying the principles of Continuous Threat Exposure Management (CTEM) and rigorous asset governance to the SaaS stack, organizations can reclaim their budget, reduce their attack surface, and build a foundation of trust with their workforce.
The data is undeniable: the companies that will lead in the next decade are not those with the most tools, but those with the most governed tools. Security is no longer a barrier to the business; it is the essential governance layer that makes the modern, hyper-integrated enterprise possible.
In the age of SaaS sprawl and “Shadow AI,” managing vendor risk is no longer optional. Emutare provides the strategic governance and asset management services needed to reclaim control of your digital ecosystem. From identifying “Zombie Applications” through rigorous IT auditing to securing autonomous workflows via AI adoption consultation, we help you move from reactive patching to continuous resilience. Secure your growth and build a “Privacy by Design” culture with our expert cybersecurity advisory.
References
- Emutare. (2025). Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM). https://insights.emutare.com/stop-patching-everything-the-case-for-continuous-threat-exposure-management-ctem/ ↩︎
- Cisco. (2025). Global Hybrid Work Study 2025. https://newsroom.cisco.com/c/dam/r/newsroom/pdfs/Cisco-Hybrid-Work-Study.pdf ↩︎
- Emutare. (2025). Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs. https://insights.emutare.com/operationalizing-trust-fixing-the-broken-feedback-loop-in-modern-socs/ ↩︎
- Google Cloud. (2026). Cybersecurity Forecast 2026. https://services.google.com/fh/files/misc/cybersecurity-forecast-2026-en.pdf? ↩︎
- Emutare. (2025). API Asset Governance: Identifying and Decommissioning Obsolete Endpoints. https://insights.emutare.com/api-asset-governance-identifying-and-decommissioning-obsolete-endpoints/ ↩︎
- Google. (2025). Google Cloud Study Reveals 52% of Executives Say Their Organizations Have Deployed AI Agents, Unlocking a New Wave of Business Value. https://www.googlecloudpresscorner.com/2025-09-04-Google-Cloud-Study-Reveals-52-of-Executives-Say-Their-Organizations-Have-Deployed-AI-Agents,-Unlocking-a-New-Wave-of-Business-Value,1 ↩︎
Related Blog Posts
- Advanced Anti-Phishing Controls and User Training: Building Resilient Cybersecurity Defenses
- Board Reporting on Cybersecurity: What Executives Need to Know
- Multi-Factor Authentication: Comparing Different Methods
- Secrets Management in DevOps Environments: Securing the Modern Software Development Lifecycle
- Zero Trust for Remote Work: Practical Implementation
- DevSecOps for Cloud: Integrating Security into CI/CD
- Customer Identity and Access Management (CIAM): The Competitive Edge for

