When “seeing is believing” becomes your biggest security vulnerability
The call came in on a Friday afternoon. The face on the video conference was familiar; it was the Chief Financial Officer. The voice was unmistakable, capturing the specific cadence and tone the finance team heard every week. The request was urgent but plausible: a secret acquisition required an immediate, discreet transfer of funds.
The employee complied. It wasn’t until $25 million had left the company accounts that the truth emerged: the CFO was never on the call. The employee had been talking to a “deepfake” — a hyper-realistic AI simulation.
This isn’t a scene from a science fiction novel. It is the reality of the 2024-2025 threat landscape. As covered by the World Economic Forum, the multinational engineering firm Arup fell victim to exactly this type of attack, proving that the era of “CEO Fraud 2.0” has arrived, as explained by Arup’s Chief, on the lessons learned from a $25m deepfake crime, “This happens more frequently than people realize.”1
For business leaders and IT professionals, this shifts the paradigm. We have spent decades teaching employees to scrutinize email headers and check for typos. But how do you train someone to doubt their own eyes and ears?
The “Trust Gap” in Modern Security
For years, Business Email Compromise (BEC) has been a top source of income for cybercriminals. But traditional BEC had a flaw: it relied on text. Smart employees could pick up the phone, call the executive, and verify the request.
Generative AI has closed that loop.
Deepfake technology has advanced to the point where attackers can clone a voice with just three seconds of audio or render a live video puppet from a few photos. According to data reported by Investopedia,2 deepfake fraud attempts surged by over 1,300% in 2024 alone. This exponential growth signals that attackers are moving away from “spray and pray” phishing to highly targeted, high-value extraction.
The psychological impact is profound. We are biologically wired to trust what we see and hear. When an authoritative figure (like a CEO) gives a direct command via video, the “obedience to authority” bias kicks in, bypassing the critical thinking centers of the brain that might otherwise flag a suspicious email.
Re-Architecting Your Defense
Defending against deepfakes requires more than just better awareness training; it requires a fundamental shift in your technology and policy architecture. We cannot rely on human intuition to spot these forgeries because the forgeries are becoming better than human perception.
Instead, we must build a “Zero Trust” approach to communication itself.
1. The Technology Layer: Identity as the New Perimeter
The first line of defense is ensuring that the person on the screen is who they claim to be. This means your Security Technology Stack for Growing Businesses must evolve. As we have discussed in previous guides, a modern stack is not just about firewalls; it is about identity assurance. To learn more about building a resilient defense architecture, you can review our guide on the Security Technology Stack for Growing Businesses.3
Implementing FIDO2-compliant hardware keys (like YubiKeys) and enforcing biometric authentication that resists “injection attacks” are critical steps. If an attacker mimics a CEO’s face but cannot produce the physical hardware key required to authorize a high-value transfer, the attack fails. A recent research, FIDO2: A comprehensive study on passwordless authentication,4 argues that traditional authentication methods are failing against modern threats. While passwords are vulnerable to phishing and breaches, inherence factors (biometrics) are increasingly susceptible to “presentation attacks,” specifically deepfakes. The paper positions FIDO2 as the necessary “possession factor” that bridges this gap, relying on physical hardware that cannot be digitally spoofed.
2. The Monitoring Layer: Catching the “Aftermath”
Deepfakes are often the “entry” move; the social engineering hook used to get credentials or access. Once the attacker is “in” (or once they have convinced an insider to move money), their behavior on the network changes. They might attempt to access lateral systems or exfiltrate sensitive data to support their extortion.
This is where your network visibility becomes the safety net. An effectively deployed Intrusion Detection System (IDS) acts as a relentless monitor for this anomalous activity. Even if the human is fooled, the network sensors should not be.
As previously covered, placing these sensors strategically, monitoring internal traffic (East-West) rather than just the perimeter (North-South), is vital for catching attackers who have already bluffed their way past the front door. You can read more about these tactical placements in our article on IDS/IPS Deployment Strategies for Maximum Effectiveness.5
3. The Strategy Layer: Prioritizing Your VIPs
Not every employee is a target for a deepfake attack. Creating a deepfake takes computing power and time. Attackers focus on “High Value Targets” (HVTs); executives, finance directors, and IT administrators with elevated privileges.
This aligns with the principles of Risk-Based Vulnerability Prioritization. Just as you prioritize patching the vulnerabilities that are most likely to be exploited, you must prioritize the human assets who are most likely to be targeted.
To learn more about focusing your limited resources where they matter most, refer to our insights on Risk-Based Vulnerability Prioritization: A Strategic Approach to Modern Cybersecurity.6
Your “human vulnerability management” should focus on these groups. They require stricter verification protocols (e.g., dual-approval for transfers over a certain amount) and more frequent, specialized training than the general staff.
Practical Implementation: The “Challenge-Response” Protocol
Technology is essential, but culture is free and immediate. One of the most effective defenses against deepfakes is the implementation of a “Challenge-Response” protocol.
This is a low-tech solution to a high-tech problem. Establish a “safe word” or a specific challenge question for your executive team and finance department.
- The Protocol: If a request for funds or sensitive data occurs via video or audio, the recipient asks the “Challenge” question.
- The Check: The answer must be something not publicly known (unlike your mother’s maiden name or high school, which are easily found on social media).
- The Fail-Safe: If the video-caller hesitates, claims they “forgot,” or tries to bypass the question with urgency (e.g., “I don’t have time for this!”), the employee is authorized to hang up immediately without fear of reprimand.
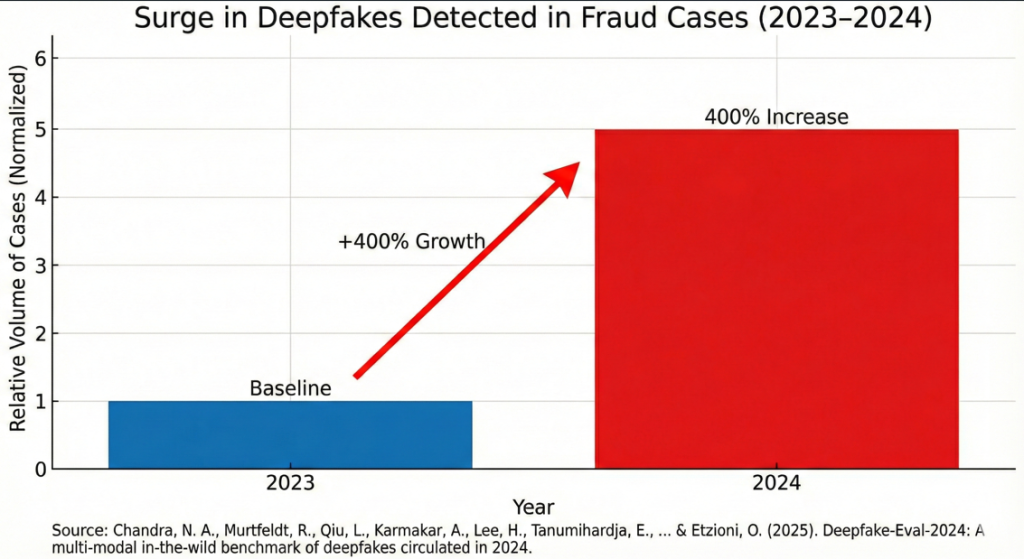
Assessing the Future Risk
The threat is not static. We are already seeing the rise of “injection attacks” where attackers bypass the camera entirely and inject pre-recorded or real-time generated footage directly into the video feed of tools like Zoom or Teams. A preliminary research released in 2025 led by researchers from the University of Washington, Deepfake-Eval-2024: A Multi-Modal In-the-Wild Benchmark of Deepfakes Circulated in 20247 highlights a critical failure in current defensive measures. In justifying the need for updated detection benchmarks, the authors cite data revealing a fourfold (400%) increase in deepfakes detected in fraud cases between 2023 and 2024. The research further exposes that widely used open-source detection models fail to catch these new “in-the-wild” attacks, with their detection accuracy (AUC) dropping by nearly 50% when tested against modern, real-world deepfakes compared to older academic datasets.
This means your endpoint protection and video conferencing software configurations must be hardened. Disallowing “virtual cameras” on sensitive devices and requiring signed application execution can mitigate some of these technical bypasses.
Conclusion
The deepfake era sounds dystopian, but it is manageable. The goal is not to stop deepfakes from existing; that is impossible, but to strip them of their power.
By combining a robust Security Technology Stack that verifies identity, an IDS/IPS Strategy that watches for the resulting anomaly, and a Risk-Based approach that protects your most targeted people, you create an environment where a fake video is just a nuisance, not a catastrophe.
We must replace blind trust with verified authenticity. In a world where you cannot believe your eyes, you must be able to trust your process.
Don’t let deepfakes turn trust into your biggest vulnerability. Emutare provides the architectural and procedural defenses you need.
Our services, including SIEM and XDR Deployment to catch anomalous network behavior, specialized Cybersecurity Awareness Training for your High Value Targets, Cybersecurity Advisory for building strong risk-management policies, and Implementation of Cybersecurity Controls, will help you shift from a culture of blind trust to one of verified authenticity.
Future-proof your security. Consult with Emutare today.
References
- World Economic Forum. (2025). Cybercrime: Lessons learned from a $25m deepfake attack. Available at: https://www.weforum.org/stories/2025/02/deepfake-ai-cybercrime-arup/ ↩︎
- Investopedia. (2025). Warren Buffett DeepFakes on TikTok—Here’s How To Spot Them Every Time. https://www.investopedia.com/spotting-warren-buffett-deepfakes-on-tiktok-11850395 ↩︎
- Emutare. (2025). Security Technology Stack for Growing Businesses. https://insights.emutare.com/security-technology-stack-for-growing-businesses/ ↩︎
- Mitra, A., & Ghosh, A. (2024). FIDO2: A comprehensive study on passwordless authentication. International Journal of Engineering Research and Applications, 14(7), 58–63. https://www.ijera.com/papers/vol14no7/14075863.pdf ↩︎
- Emutare. (2025). IDS/IPS Deployment Strategies for Maximum Effectiveness. https://insights.emutare.com/ids-ips-deployment-strategies-for-maximum-effectiveness/ ↩︎
- Emutare. (2025). Risk-Based Vulnerability Prioritization: A Strategic Approach to Modern Cybersecurity. https://insights.emutare.com/risk-based-vulnerability-prioritization-a-strategic-approach-to-modern-cybersecurity/ ↩︎
- Chandra, N. A., Murtfeldt, R., Qiu, L., Karmakar, A., Lee, H., Tanumihardja, E., Farhat, K., Caffee, B., Paik, S., Lee, C., Choi, J., Kim, A., & Etzioni, O. (2025). Deepfake-Eval-2024: A multi-modal in-the-wild benchmark of deepfakes circulated in 2024. arXiv. https://arxiv.org/pdf/2503.02857 ↩︎
Related Blog Posts
- Cybersecurity Essentials for Startups: Safeguarding Your Business from Digital Threats
- Insider Threats: Detection and Prevention Strategies
- Securing Microsoft 365 Email Environments: A Comprehensive Guide
- Crisis Communication During Security Incidents: A Strategic Approach
- Building a Security Operations Center (SOC): Key Components
- Implementing Single Sign-On: Pros, Cons, and Best Practices
- Backup and Recovery: Building Resilience Against Ransomware

