The modern enterprise is no longer a self-contained fortress; it is a single node in a vast, interconnected digital ecosystem. While most organizations have made strides in assessing their direct (Tier-1) vendors, the true risk often lies buried deep within the “Nth-degree” of the supply chain. A vulnerability in a small, third-tier software library or a breach at a fourth-tier managed service provider can cascade upward, resulting in a systemic failure for the primary organization.
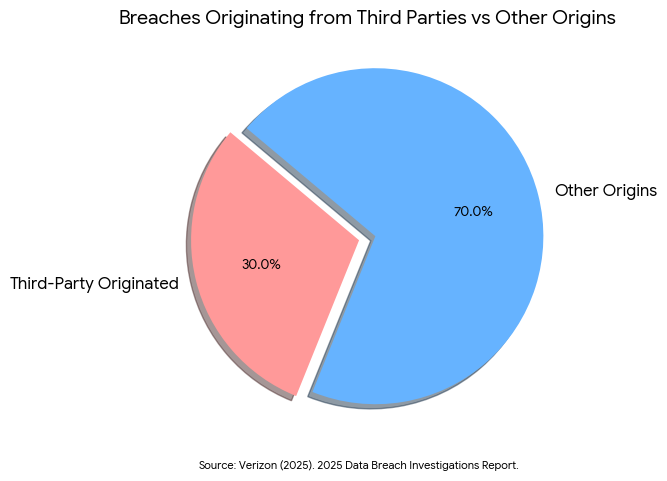
As we navigate 2026, the complexity of these dependencies has reached a critical mass. The “Tier-N” problem is no longer just a supply chain issue; it is a primary cybersecurity threat. The 2025 DBIR1 signals the end of the ‘perimeter’ as we knew it. With 30% of breaches now originating from third parties and an increase in edge-device exploits, security is no longer just about your own walls, it’s about the integrity of every vendor and device connected to your network. This article explores why legacy vendor management is failing and provides a strategic blueprint for achieving deep-tier visibility to ensure long-term resilience.
The Illusion of Control: Why Tier-1 Assessments Are Not Enough
Historically, vendor risk management (VRM) has been a linear process. Organizations send security questionnaires to their direct partners, review their SOC 2 reports, and assume the risk is contained. However, this “point-in-time” approach creates a false sense of security. Your direct vendor (Tier-1) relies on a cloud provider (Tier-2), who utilizes a specialized analytics engine (Tier-3), which may be built on an open-source library maintained by a single developer (Tier-N).
As previously covered in Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM),2 security is about reachability. If an attacker can compromise a Tier-3 provider and use that access to pivot into your environment, it does not matter how secure your Tier-1 vendor’s headquarters is. The industry is waking up to the reality that many organizations have a relationship with a third party that has experienced a breach, often without the primary organization even being notified.
This “visibility gap” is a force multiplier for cybercriminals. According to Supply Chain Characteristics as Predictors of Cyber Risk: A Machine-Learning Assessment,3 researchers applied machine learning models to examine whether supply chain network characteristics improve the prediction of cyber breach risk. The study finds that incorporating features related to an organization’s supply chain relationships significantly enhances predictive accuracy compared to relying on firm specific attributes alone. These incidents are particularly dangerous because they often trigger multiple, simultaneous organizational failures across different sectors, making coordination and recovery exponentially more difficult.
Operationalizing Trust Across the Value Network
Managing the Nth-degree requires a shift in how we define “trust.” In a fragmented ecosystem, trust cannot be a static attribute; it must be an operational constant. The challenge for modern SOCs is that they are often “flying blind” regarding the security posture of the sub-tier vendors that their primary partners rely on.
As previously covered in Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs,4 trust is broken when there is a disconnect between finding a risk and fixing it. In the context of the supply chain, this means that even if a Tier-2 vulnerability is identified, the communication channel to remediate it often doesn’t exist. This lack of a feedback loop between tiers is why supply chain incidents now cost 17 times more to remediate than first-party breaches.
The cost of this disconnect is staggering. According to the Federal Bureau of Investigation’s press release titled “FBI Releases Annual Internet Crime Report,”5 the FBI’s Internet Crime Complaint Center (IC3) reported that in 2024 total reported cybercrime losses in the United States exceeded $16.6 billion, marking a significant increase from the previous year. The 2024 Internet Crime Report combines information from over 859,000 complaints of suspected internet crime and highlights the growing financial impact of online fraud, scams, and other cyber-enabled offenses.
These costs are driven not just by the breach itself, but by the complexity of multi-party investigations where no single entity has visibility into the entire “chain of custody” for the data.
API Governance: The Connective Tissue of Tier-N Risk
If the supply chain is the body of the modern enterprise, APIs are the nervous system. They are the primary method by which data flows between Tier-1, Tier-2, and Tier-N providers. However, this interconnectedness creates a massive, silent attack surface. An API endpoint managed by a sub-vendor may remain active long after the business relationship has ended, providing a “Zombie” access point for attackers.
Rigorous API Asset Governance: Identifying and Decommissioning Obsolete Endpoints6 is the only way to secure the Nth-degree. Governance teams must look beyond their own internal APIs and begin auditing the “external” APIs that their vendors are using to process company data. If a Tier-1 vendor is using an insecure Tier-2 API, that is a direct risk to your organization.
Cyber risk no longer lives inside the firewall. For public and private sector leaders alike, the mission now depends on managed service providers and software suppliers that sit outside their direct control. Managing these relationships requires “embeddedness,” integrating resilience deeply within the organizational processes and culture of every collaborator in the value chain.
Implementation Guidance: Mapping the Nth-Degree
Achieving Tier-N visibility is an incremental process that moves from simple contract management to active, automated orchestration.
Phase 1: Criticality Mapping and Dependency Discovery
You cannot map the entire world at once. Start with your most vital business functions.
- Identify Crown Jewels: Which data sets or services, if compromised, would result in immediate business failure?
- Request Sub-Vendor Lists: Mandate that Tier-1 vendors disclose their “Critical Sub-Processors” as part of their contract.
- Use Passive Discovery: Leverage external security rating tools to identify the infrastructure and cloud providers actually used by your partners, verifying their self-reported data.
Phase 2: Implementing SBOMs and IBOMs
Software Bill of Materials (SBOM) and Infrastructure Bill of Materials (IBOM) are the “nutrition labels” of the digital age.
- Standardize Formats: Require all software vendors to provide machine-readable SBOMs (e.g., CycloneDX or SPDX).
- Automate Ingestion: Use tools to cross-reference your SBOM library against new vulnerability disclosures in real-time. If a Tier-3 library is compromised, you should know within minutes if you are affected.
Phase 3: Contractual “Flow-Down” Requirements
Security is a legal obligation as much as a technical one.
- Enforce Security Standards: Include “Right to Audit” and “Security Flow-Down” clauses in contracts, requiring Tier-1 vendors to enforce your security standards on their own sub-vendors.
- Continuous Monitoring Clauses: Shift from annual reviews to a requirement for “Continuous Monitoring” and “Real-time Incident Notification.”
Phase 4: Collaborative “Coopetition”
In 2026, resilience is a team sport.
- Share Threat Intel: Work with industry peers to identify “High-Risk Nth-Party Nodes,” the common providers that many companies depend on.
- Joint Cyber Exercises: Conduct simulation exercises that include your Tier-1 and key Tier-2 partners to test incident response coordination across the network.
Conclusion
The “Nth-degree” is where the next major breach is currently hiding. In a world where many organizations experienced at least one supply chain breach in 2025, the old model of “trust but verify” only Tier-1 vendors is no longer viable. We must transition to a model of continuous, deep-tier visibility where governance, API hygiene, and operational trust are extended across the entire value network.
By mastering Tier-N visibility, business leaders move from being reactive victims of cascading failures to proactive orchestrators of a resilient ecosystem. The complexity of the modern digital supply chain is an advantage only if it is governed; otherwise, it is a liability that scales faster than any human defense.
Secure Your Digital Ecosystem with Emutare
Don’t let the Nth degree be your blind spot. Emutare bridges the visibility gap by operationalizing trust across your entire value network. Our platform automates SBOM ingestion and provides rigorous API Asset Governance to eliminate zombie endpoints and silent vulnerabilities. We help you move beyond point-in-time assessments toward Continuous Threat Exposure Management, ensuring your security standards flow down to every sub-vendor. Transform your supply chain from a scaling liability into a resilient strategic advantage.
References
- Verizon. (2025). 2025 Data Breach Investigations Report. https://www.verizon.com/business/resources/Tbb1/reports/2025-dbir-data-breach-investigations-report.pdf ↩︎
- Emutare. (2025). Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM). https://insights.emutare.com/stop-patching-everything-the-case-for-continuous-threat-exposure-management-ctem/ ↩︎
- Hu, K., Levi, R., Yahalom, R., & Zerhouni, E. G. (2022). Supply chain characteristics as predictors of cyber risk: A machine-learning assessment. arXiv. https://arxiv.org/abs/2210.15785 ↩︎
- Emutare. (2025). Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs. https://insights.emutare.com/operationalizing-trust-fixing-the-broken-feedback-loop-in-modern-socs/ ↩︎
- Federal Bureau of Investigation. (2025). FBI Releases Annual Internet Crime Report. https://www.fbi.gov/news/press-releases/fbi-releases-annual-internet-crime-report? ↩︎
- Emutare. (2025). API Asset Governance: Identifying and Decommissioning Obsolete Endpoints. https://insights.emutare.com/api-asset-governance-identifying-and-decommissioning-obsolete-endpoints/ ↩︎
Related Blog Posts
- SOC 2 Compliance: Preparation and Audit Process
- Azure Security Best Practices for Australian Businesses: A Comprehensive Guide for 2025
- Tabletop Exercises: Testing Your Incident Response Plan
- BGP Security: Protecting Your Internet Routing
- Data-Centric Security Architecture: Building Resilience Through Data-Focused Protection
- Network Security Zoning and Segmentation Design: Building Resilient Digital Perimeters in 2025
- Threat Intelligence Sharing: Communities and Frameworks

