The modern Security Operations Center (SOC) is currently battling a silent epidemic. As digital environments expand into complex multi-cloud architectures and agentic AI ecosystems, the volume of security telemetry has reached a point that no human team can realistically process. Traditional security information and event management (SIEM) systems act as sirens, wailing for every anomaly, but providing little clarity on which ones are truly dangerous. This has led to “Alert Fatigue,” a state of sensory overload where security analysts become desensitized to warnings, increasing the risk of missing a genuine breach.
By 2026, the solution is no longer just “better filtering.” The industry is shifting toward Predictive Contextualization. This approach uses artificial intelligence to not only prioritize alerts but to predict their potential impact by enriching them with real-time business context and historical attack patterns. To cure alert fatigue, business leaders must move from a reactive “alert-centric” model to a proactive “operation-centric” model. This article provides actionable insights for IT professionals to implement predictive frameworks that transform noise into decisive intelligence.
The Human Cost of the “Noise Floor”
Alert fatigue is not just a technical problem; it is a significant contributor to SOC analyst burnout and high turnover rates. When analysts spend their entire shift triaging thousands of low-fidelity alerts, most of which are false positives, they lose the capacity for deep investigative work. According to the Cisco 2025 Global State of Security Report,1 SOC teams are facing sustained operational strain. Over half of security professionals report being overworked, and a similar proportion say stress has made them consider leaving the field. The report also highlights unrealistic expectations from leadership as a contributing factor, reinforcing concerns about burnout, retention challenges, and long term workforce sustainability within security operations.
As previously covered inOperationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs,2 trust is eroded when security teams are overwhelmed. If the “Feedback Loop” between the SOC and the engineering team is clogged with irrelevant data, remediation slows down, and the organization’s overall security posture suffers. Curing alert fatigue requires a system that understands not just that an event happened, but why it matters to the specific business context.
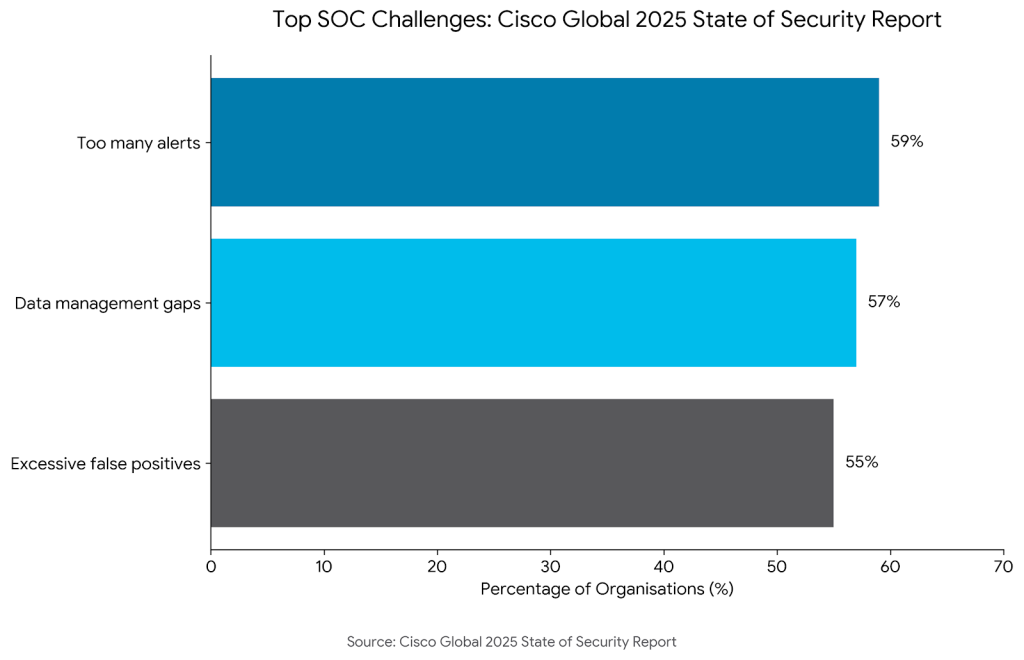
In the Cisco Global 2025 State of Security Report Cisco3 highlights serious SOC challenges, reporting that 57% of organisations say they lose valuable investigation time due to data management gaps, 59% have too many alerts, and 55% struggle with excessive false positives in their workflows. Without predictive prioritization, the SIEM effectively becomes a “data graveyard” rather than a tool for defense.
From Reactive Filtering to Predictive Contextualization
Predictive contextualization represents a departure from the “Boolean” logic of traditional scanners (where a vulnerability is either present or absent). Instead, it uses machine learning to assign a “Probability of Impact.” By correlating an alert with the asset’s business value, the user’s behavioral history, and current threat intelligence, the system can predict whether an anomaly is a routine administrative task or the early stages of a ransomware campaign.
To learn more about how this prioritization fits into a broader strategy,Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM)4 explains that organizations must focus on “reachability.” Predictive models can simulate attack paths in real-time, effectively silencing alerts for vulnerabilities that are shielded by other layers of defense. This reduces the “noise floor,” allowing analysts to focus on the 1% of alerts that represent a true threat.
This technical evolution suggests that organizations adopting Exposure Management (CEM) will be less likely to experience a breach by 2026. By predicting which exposures an attacker is most likely to target, organizations can remediate risks before an alert is even triggered.
API Governance: The Context Engine
One of the primary sources of “alert noise” in 2026 is the surge of API-to-API communication. In a microservices environment, a single user action can trigger dozens of internal API calls, many of which may look anomalous to a poorly tuned monitor. Predictive contextualization requires a deep understanding of these connections.
Rigorous API Asset Governance: Identifying and Decommissioning Obsolete Endpoints5 serves as the “context engine” for the SOC. If an alert is triggered by an API that has been officially decommissioned but is still receiving traffic, the system should immediately flag it as a high-priority “Zombie API” event. Conversely, if an alert comes from a known, low-risk internal service, the predictive model can automatically deprioritize it, saving hours of manual investigation.
The AI-Driven Guided Response for Security Operation Centers with Microsoft Copilot for Security6 introduces Microsoft Copilot for Security Guided Response, an AI system designed to support Security Operations Centers by contextualizing incidents rather than treating alerts individually. It uses historical incident data to identify similar past cases, assist with triage decisions, and recommend remediation steps. By embedding contextual insights directly into the workflow, the system helps analysts construct a coherent view of multi-stage attacks while reducing alert fatigue and cognitive load.
Implementation Guidance: A 4-Step Roadmap to Curing Fatigue
Business leaders can implement a predictive contextualization framework by following this structured roadmap:
1. Asset Criticality Mapping
Predictive models are only as good as the data they consume. You must define what matters most to your business.
- Tier Assets: Classify every server, database, and API based on its business impact (e.g., Tier 1 for customer-facing payment systems).
- Automate Discovery: Use continuous asset discovery to ensure the “Context Engine” has an up-to-date map of your environment.
2. Enrichment at Source
Do not wait for an alert to reach the SIEM to enrich it. Enrichment should happen as close to the data source as possible.
- Integrate Threat Intel: Feed real-time feeds into your EDR and NDR tools to instantly tag alerts with known adversary signatures.
- Add Identity Context: Link every alert to a specific user identity and device health status to differentiate between a stolen credential and a legitimate login from a new location.
3. Implement “Confidence Scoring”
Move away from “High/Medium/Low” severity. Use a 0-100 confidence score based on multiple variables.
- Variable Weighting: Weight scores based on asset criticality, vulnerability exploitability, and the presence of compensating controls.
- Suppression Logic: Automatically suppress alerts with a confidence score below a certain threshold, sending them to a “low-priority” queue for weekly review rather than immediate triage.
4. Establish a Feedback Loop for Model Tuning
Predictive models require constant refinement to remain accurate.
- Analyst Feedback: Enable a “thumbs up/down” feature for SOC analysts to grade the accuracy of an alert’s prioritization.
- Retrain Regularly: Use this feedback to retrain the underlying machine learning models every quarter, ensuring they adapt to changes in your environment and emerging threat tactics.
Conclusion
Curing alert fatigue is no longer a luxury; it is a fundamental requirement for operational resilience in 2026. By moving beyond traditional filtering and embracing predictive contextualization, organizations can protect their most valuable asset: their security talent. When analysts are empowered by AI that understands business context, they stop being “alert cleaners” and start being “strategic defenders.”
The transition to predictive security requires a commitment to asset governance, operational trust, and the continuous management of exposure. In a world where attackers move at machine speed, our defenses must not only keep up, they must anticipate the next move before the first siren even sounds.
To silence the noise of alert fatigue, organizations need more than just filters, they need predictive intelligence. Emutare delivers this through SIEM and XDR Deployment, transforming raw telemetry into high-confidence, actionable insights. Our AI Adoption and Technology Consultation empowers your team with machine-learning models that predict impact based on your unique business context. Coupled with rigorous IT Asset and Patch Management, we ensure your “Context Engine” remains accurate and resilient. Let Emutare help you transition from reactive triaging to proactive, operation-centric defense today.
References
- Cisco. (2025). Cisco 2025 Global State of Security Report. https://investor.cisco.com/news/news-details/2025/Global-State-of-Security-Report-Reveals-Critical-Need-for-Connected-Security-Operations/default.aspx? ↩︎
- Emutare. (2026). Operationalizing Trust: Fixing the Broken Feedback Loop in Modern SOCs. https://insights.emutare.com/operationalizing-trust-fixing-the-broken-feedback-loop-in-modern-socs/ ↩︎
- Cisco. (2025). Cisco 2025 Global State of Security Report. https://investor.cisco.com/news/news-details/2025/Global-State-of-Security-Report-Reveals-Critical-Need-for-Connected-Security-Operations/default.aspx? ↩︎
- Emutare. (2026). Stop Patching Everything: The Case for “Continuous Threat Exposure Management” (CTEM). https://insights.emutare.com/stop-patching-everything-the-case-for-continuous-threat-exposure-management-ctem/ ↩︎
- Emutare. (2025). API Asset Governance: Identifying and Decommissioning Obsolete Endpoints. https://insights.emutare.com/api-asset-governance-identifying-and-decommissioning-obsolete-endpoints/ ↩︎
- Freitas, S., Kalajdjieski, J., Gharib, A., & McCann, R. (2024). AI-driven guided response for security operation centers with Microsoft Copilot for Security. arXiv. https://arxiv.org/pdf/2407.09017 ↩︎
Related Blog Posts
- Advanced Anti-Phishing Controls and User Training: Building Resilient Cybersecurity Defenses
- Board Reporting on Cybersecurity: What Executives Need to Know
- Multi-Factor Authentication: Comparing Different Methods
- Secrets Management in DevOps Environments: Securing the Modern Software Development Lifecycle
- Zero Trust for Remote Work: Practical Implementation
- DevSecOps for Cloud: Integrating Security into CI/CD
- Customer Identity and Access Management (CIAM): The Competitive Edge for Australian Businesses

